Sheesh, the US is sure getting scary. Well, it's a good thing it would be impossible to trace Signal to someone via metadata like a phone number, right?
Even State Department-funded Human Rights Watch admits that authorities combine legal and illegal methods to obtain convictions: text.hrw.org/report/2018/01/09…
Combining dragnet surveillance with device hacking is intended in the design of both tools. Hence, State Department-funded Signal dupes you into handing over your identity as part of the population-centric mapping. In custody, your phone will be hacked when it is taken away if it's important.
This entry was edited (1 week ago)
like this

Natanael
in reply to DJ Putler • • •rezz
in reply to Natanael • • •TwiddleTwaddle
in reply to rezz • • •SreudianFlip
in reply to TwiddleTwaddle • • •DJ Putler
in reply to TwiddleTwaddle • • •Dessalines
in reply to TwiddleTwaddle • • •wildbus8979
in reply to Natanael • • •Natanael
in reply to wildbus8979 • • •At that point you can rely on nothing but Tor or I2P
Nothing else hides metadata better than Signal, without involving large networks of independent nodes that participate in Sybil resistant routing. The only thing that gets close is threshold schemes where you still need multiple independent entities running servers.
akilou
in reply to Natanael • • •TheLeadenSea
in reply to akilou • • •parzival
in reply to TheLeadenSea • • •Natanael
in reply to akilou • • •DJ Putler
in reply to Natanael • • •akilou
in reply to DJ Putler • • •Hominine
in reply to akilou • • •DJ Putler
in reply to Hominine • • •Hominine
in reply to DJ Putler • • •DJ Putler
in reply to akilou • • •Undearius
in reply to DJ Putler • • •theherk
in reply to DJ Putler • • •Natanael
in reply to theherk • • •It does use deniable encryption, but that stops working as a defense the second they take your phone and copy all logs from your device.
And large group chats relies on how well you can vet participants more than it relies on encryption itself, and if they're too large they may as well not be encrypted.
MeowZedong
in reply to Natanael • • •nooch
in reply to Natanael • • •/home/pineapplelover
in reply to nooch • • •James R Kirk
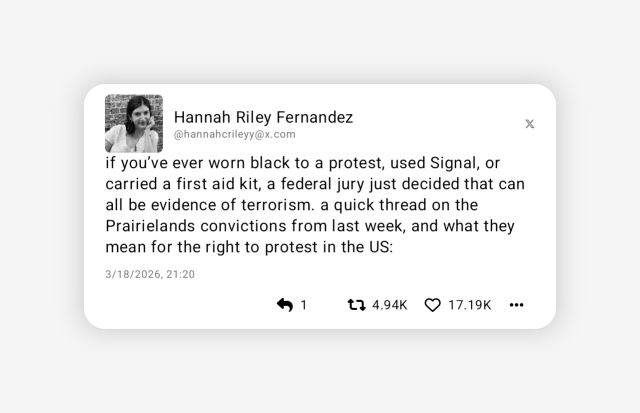
in reply to DJ Putler • • •This is total alarmist misinformation. The "evidence of terrorism" was not "using Signal" or "carrying a first aid kit", it was taking part in an armed assault on an immigration facility where a dozen people set off fireworks and shot a police officer with an AR-15.
The prosecution used the presence of the first aid kit they carried during their armed assault, along with actual messages (not metadata) from a Signal chat to make the case that the attackers planned on using violence.
There are a lot of problems with this case, IMO the most dangerous part here is that adds legitimacy the (false) idea that "antifa" is an organization that exists. Something the Trump administration has been struggling to prove. This X post takes small details out of context.
Xaphanos
in reply to James R Kirk • • •Skullgrid
in reply to James R Kirk • • •based
like this
Liberta likes this.
astraeus
in reply to Skullgrid • • •Eager Eagle
in reply to astraeus • • •Better World
in reply to Skullgrid • • •☆ Yσɠƚԋσʂ ☆
in reply to James R Kirk • • •DJ Putler
in reply to James R Kirk • • •IDK why it is alarmist misinformation to point out that the people doing this have the strongest spyware/phone cracking tools in the world, information about who owns phone numbers, access to AWS (a US military contractor currently being affected by a not insignificant missile-induced service outages), access to Firebase and Apple Websocket (latter has poor encryption and I have heard the former is also insecure), and the ability to physically bring you into custody, then lie about how they got all of these elements together in whatever order to get you behind bars. But of course the idea of actually doing something about the gestapo in your country just fills you with indignation apparently.
X is actually the only place that you can still hear from a lot of people, like Julie K Brown a Miami Herald journalist writing about Jeffrey Epstein's associates and their victims, thousands of foreign journalists. That probably isn't important to you since it isn't about Star Trek and toys. I get all of the posts through a server called RSSHub combined with numerous other websites (li
... Show more...IDK why it is alarmist misinformation to point out that the people doing this have the strongest spyware/phone cracking tools in the world, information about who owns phone numbers, access to AWS (a US military contractor currently being affected by a not insignificant missile-induced service outages), access to Firebase and Apple Websocket (latter has poor encryption and I have heard the former is also insecure), and the ability to physically bring you into custody, then lie about how they got all of these elements together in whatever order to get you behind bars. But of course the idea of actually doing something about the gestapo in your country just fills you with indignation apparently.
X is actually the only place that you can still hear from a lot of people, like Julie K Brown a Miami Herald journalist writing about Jeffrey Epstein's associates and their victims, thousands of foreign journalists. That probably isn't important to you since it isn't about Star Trek and toys. I get all of the posts through a server called RSSHub combined with numerous other websites (like this one), which are piped directly into an actually secure messaging service. I encourage any admins to get my posts hidden from their entire instance. Don't let your users come into my mentions! I wish that blocking instances actually WORKED. 💀
mfed1122
in reply to DJ Putler • • •DJ Putler
in reply to mfed1122 • • •Do you think they won't do the same to my favorite apps?
CIA-funded outlet The Intercept here points out the CIA considers Signal software for terrorists and later recommended "highly-targeted individuals" use it (these are both endorsements to different audiences). Since e2ee software is viewed as a threat, how should we take the US govt singling out Signal for endorsement like this? Is the CIA being nice and helpful? web.archive.org/theintercept.c…
U.S. Officials Called Signal a Tool for Terrorists and Criminals. Now They’re Using It.
Matt Sledge (The Intercept)mfed1122
in reply to DJ Putler • • •quick_snail
in reply to James R Kirk • • •BradleyUffner
in reply to quick_snail • • •0_o7
in reply to James R Kirk • • •How did they get the actual messages? Signal chats and groups are supposed to be encrypted. I'm curious.
MalReynolds
in reply to 0_o7 • • •Most likely had someone in the group chat (opsec issue) or captured a phone and made the owner open it.
xkcd.com/538/
Security
xkcd☆ Yσɠƚԋσʂ ☆
in reply to DJ Putler • • •A reminder that your phone number is metadata. And people who think metadata is "just" data or that cross-referencing is some kind of sci-fi nonsense, are fundamentally misunderstanding how modern surveillance works.
By requiring phone numbers, Signal, despite its good encryption, inherently builds a social graph. The server operators, or anyone who gets that data, can see a map of who is talking to whom. The content is secure, but the connections are not.
Being able to map out who talks to whom is incredibly valuable. A three-letter agency can take the map of connections and overlay it with all the other data they vacuum up from other sources, such as location data, purchase histories, social media activity. If you become a "person of interest" for any reason, they instantly have your entire social circle mapped out.
Worse, the act of seeking out encrypted communication is itself a red flag. It's a perfect filter: "Show me everyone paranoid enough to use crypto." You're basically raising your hand.
So, in a twisted way, Signal being a tool for private conv
... Show more...A reminder that your phone number is metadata. And people who think metadata is "just" data or that cross-referencing is some kind of sci-fi nonsense, are fundamentally misunderstanding how modern surveillance works.
By requiring phone numbers, Signal, despite its good encryption, inherently builds a social graph. The server operators, or anyone who gets that data, can see a map of who is talking to whom. The content is secure, but the connections are not.
Being able to map out who talks to whom is incredibly valuable. A three-letter agency can take the map of connections and overlay it with all the other data they vacuum up from other sources, such as location data, purchase histories, social media activity. If you become a "person of interest" for any reason, they instantly have your entire social circle mapped out.
Worse, the act of seeking out encrypted communication is itself a red flag. It's a perfect filter: "Show me everyone paranoid enough to use crypto." You're basically raising your hand.
So, in a twisted way, Signal being a tool for private conversations, makes it a perfect machine for mapping associations and identifying targets. The fact that it operates using a centralized server located in the US should worry people far more than it seems to.
The kicker is that thanks to gag orders, companies are legally forbidden from telling you if the feds come knocking for this data. So even if Signal's intentions are pure, we'd never know how the data it collects is being used. The potential for abuse is baked right into the phone-number requirement.
davel
in reply to ☆ Yσɠƚԋσʂ ☆ • • •WhisperSystems/whispersystems.org
GitHub☆ Yσɠƚԋσʂ ☆
in reply to davel • • •TyrionBean
in reply to DJ Putler • • •Voxel
in reply to TyrionBean • • •Snot Flickerman
in reply to Voxel • • •SreudianFlip
in reply to Snot Flickerman • • •TL;DR:
virtual network extending a single private network across a public network like the Internet, appearing to users as a private network
Contributors to Wikimedia projects (Wikimedia Foundation, Inc.)Voxel
in reply to SreudianFlip • • •It is not a domain registrar, they literally say it in their FAQ.
njal.la/faq/
You do not own the domain then either.
Njalla — FAQ
njal.laSreudianFlip
in reply to Voxel • • •TyrionBean
in reply to Voxel • • •Lussy [he/him, des/pair]
in reply to DJ Putler • • •lol
The laws are made up and we’ve always been fucked. We always knew that
sakuraba
in reply to Lussy [he/him, des/pair] • • •TheLastHero [he/him]
in reply to Lussy [he/him, des/pair] • • •davel
in reply to DJ Putler • • •Some people are very protective of Signal.
- Reason: Disinformation
- Reason: privacy rule #3: "Try to keep things on topic"
- Reason: Misinfo, alarmism
- Reason: This is harmful disinformation
Why not Signal?
Why not Signal?
essaysPrettyFlyForAFatGuy
in reply to davel • • •choco_crispies
in reply to PrettyFlyForAFatGuy • • •SreudianFlip
in reply to choco_crispies • • •The essay being linked to was posted (authored?) by dessalines from lemmy.ml
You may have missed the sarcasm.
gnuthing [they/them]
in reply to DJ Putler • • •Unless I turned off the USB port...
Collatz_problem [comrade/them]
in reply to gnuthing [they/them] • • •gnuthing [they/them]
in reply to Collatz_problem [comrade/them] • • •If you have info about someone getting a graphene phone to turn the USB back on, please share as I'd like to read about it.
I don't think saying the state can torture us for info is a phone security issue per se. Especially since the only way to avoid imperial state violence is to shut up and do nothing and hope they don't come for you anyway
DJ Putler
in reply to gnuthing [they/them] • • •I wouldn't bet my life on GrapheneOS in person despite being a fan of the project due to wanting to treat my phone as a computer
*actually forgot to mention they charged the duress password guy with destruction of evidence this isn't speculative at all lmao
f3nyx
in reply to DJ Putler • • •personally, my bet is that they don't have anyone qualified enough to pull off an exploit like that (on me).
the problem with my bet: what we've seen is that they won't care, and accuse individuals of terrorism based off the color of their clothes.
DJ Putler
in reply to f3nyx • • •f3nyx
in reply to DJ Putler • • •hardware vulnerabilities undoubtedly exist, whether intentional or not. its simply the nature of designing these complex semiconductors.
that said, if one company intentionally creates a backdoor, won't they all? what phone do you buy at that point?
any startup or small phone company may not have intentional backdoors, but I can guarantee their hardware security on all other levels pales to what apple and google can accomplish. I think the question then becomes are you more worried about google having a backdoor, or about third party compromises?
im not a fan of our choices, there is no silver bullet.
Salah [ey/em]
in reply to f3nyx • • •gnuthing [they/them]
in reply to DJ Putler • • •Yeah tails does have graphene beat, but a lot of folks see a phone as a necessity. Graphene is best if you're gonna have a phone. It can turn off the USB port where it can't even be charged without being off. It can reboot itself if not unlocked frequently enough, putting the phone back into a BFU state.
Now it's possible that there's some exploit a state knows that is not public, but the software they generally use does not work on graphene as long as you are not running a pre-2022 version of graphene. Someone else mentioned rubber-hose cryptanalysis, but like if I'm getting beat for my unlock, then what do I care about getting charged with destruction of evidence?
floquant
in reply to DJ Putler • • •Manifish_Destiny
in reply to floquant • • •rumba
in reply to floquant • • •All giving out your number provides is that you have ever used Signal.
They're saying ever using a private chat service is terrorism. That's not really on Signal.
floquant
in reply to rumba • • •All your phone number provides is that you have ever used signal? Not what tower you're connected to and therefore approximate realtime location? Your full identity via your telco? Social graph and history of your calls and texts?
I'm not saying it's their fault or that they are volunteering any information, but that's how it is for any US-based corporation (doesn't matter if it's a nonprofit, any legal entity that can be subpoenaed)
xthexder
in reply to floquant • • •SpookyBogMonster
in reply to xthexder • • •They used to publish them in big books, even
☂️-
in reply to xthexder • • •that's precisely why you should not trust services that require it as private. phone number = identification.
plus apparently your government considers you a terrorist if you do.
rumba
in reply to floquant • • •If the only data surfacable from Signal is the phone number, not the crypto conversation, they didn't source you on signal and get your number, they got your number through other means and used it to prove you use signal.
They can't see the conversation to contents to supoena the number to id.
jabberwock
in reply to floquant • • •This is fundamentally not how Signal works, but you are generally correct in that a phone number has been shown to provide a lot of context for a person (or a device, at least). But Signal (the app) only uses a phone number for initial verification of an account. You have a lot of options to break that association with you - use a landline and get a call verification code, use a VoIP number (assuming you trust the provider), use a burner SIM, etc.
Once you have an account, you can choose to identify yourself on the network solely via username so the registration number is not presented to other users. The Signal protocol itself is well-audited and generally secure.
If your issue is with Signal the American company, use an open source fork like Molly with your own UnifiedPush instance. Then you're only trusting them with transport of your encrypted messages, which again have shown to be secure at least in public audits.
WhyJiffie
in reply to jabberwock • • •Paulemeister
in reply to WhyJiffie • • •WhyJiffie
in reply to Paulemeister • • •exactly. what is the question?
also its not "monitor me" and "monitor you", but "monitor whoever is using the service" more closely, and as it seems, retaliate against them.
Paulemeister
in reply to WhyJiffie • • •The question is: What privacy do I loose by signing up to Signal with a phone number instead of hypothetically a username.
If you are being monitored, they know your phone number. With that they know you are using Signal, but nothing more. Messaging through Signal is safe.
If you are not being monitored, nobody knows you are using Signal. Messaging through Signal is safe
WhyJiffie
in reply to Paulemeister • • •if you could sign up with a username, your account couldn't be linked to a real world identity. also the government wouldn't have a phone number to send state malware to (unlike signal the telephony system is full of security vulnerabilities)
if you personally are monitored then yes they know your phone number. but here it's the other way around. you became a person of interest because you use signal.
no. everybody who has the power to issue data requests to signal, and also has access to a database binding phone numbers to identities, knows that you are using signal.
Paulemeister
in reply to WhyJiffie • • •WhyJiffie
in reply to Paulemeister • • •rumba
in reply to jabberwock • • •I was putting my kid on Signal to join the family chat, he didn't have service, so we just used wifi. I don't know for sure that this hasn't changed, but when I tried, they refused a google voice account and also refused an sms api acct. I dug into it some more and it appears you have to install it on a phone with cellular service, it needs to read your phone's ID.
I tried deactivating my phone, activating his acct on my phone with Google Voip, then moving it to his tablet. It would work for about a week then stop.
I dug through a bunch of reddit and group threads on it, you simply could not activate it without a real SMS and a cellular link with all the ID's.
We eventually got him an apple watch with service, and it allowed that SMS in concert with my phone. Then I installed on his tablet and put my phone back to me. Once in a blue moon, it'll make him reverify with SMS from the watch, but it works and doesn't require my phone with service anymore.
It might just be something about google's voip which a lot places refuse, but it also refused twillio.
☂️-
in reply to floquant • • •i'm convinced the big push for signal is a CIA op. not that it's necessarily signal's fault, it could be and it could not, but setting signal as the defacto private alternative is weird.
better than whatsapp at least i guess, but that's a low ass bar to clear.
Dessalines
in reply to ☂️- • • •We know it's an op, RFA does damage control for signal:
mister_flibble
in reply to floquant • • •Ildsaye [they/them]
in reply to DJ Putler • • •migo
in reply to Ildsaye [they/them] • • •CrypticCoffee
in reply to Ildsaye [they/them] • • •Ildsaye [they/them]
in reply to CrypticCoffee • • •quick_snail
in reply to CrypticCoffee • • •Jankatarch
in reply to DJ Putler • • •حمید پیام عباسی
in reply to DJ Putler • • •minorkeys
in reply to DJ Putler • • •minorkeys
in reply to DJ Putler • • •RosaLuxemburgsGhost
in reply to DJ Putler • • •Evotech
in reply to DJ Putler • • •WorldsDumbestMan
in reply to DJ Putler • • •