Search
Items tagged with: litellm
#LiteLLM Compromised! LiteLLM - a popular Python Library used by a lot of AI tooling got compromised on PyPI, and the malicious versions are stealing everything they can find on your machine:
👇
xda-developers.com/popular-pyt…
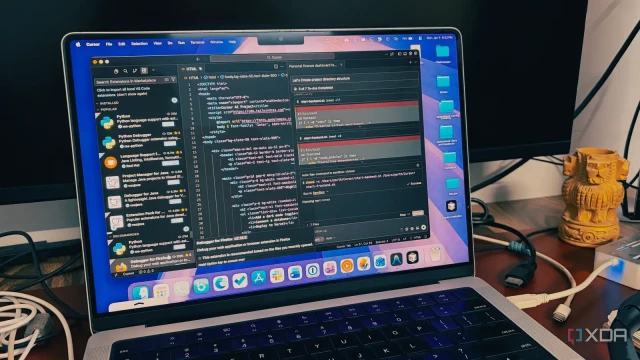
A popular Python library just became a backdoor to your entire machine
Supply chain attacks feel like they're becoming more and more common.Adam Conway (XDA)
⚠️ LiteLLM backdoored
「 On March 24, 2026, version 1.82.8 of LiteLLM was pushed to PyPI containing a malicious .pth file called "litellm_init.pth". That file executes automatically on every Python process startup, meaning you don't even need to import the library for it to run. What's more, version 1.82.7 has also been compromised. On the latest version, simply having it installed is enough, but 1.82.7 requires an import for the payload to activate 」
xda-developers.com/popular-pyt…
A popular Python library just became a backdoor to your entire machine
Supply chain attacks feel like they're becoming more and more common.Adam Conway (XDA)
Supply-chain attack on litellm
"At 10:52 UTC on March 24, 2026, litellm version 1.82.8 was published to PyPI. The release contains a malicious .pth file (litellm_init.pth) that executes automatically on every Python process startup when litellm is installed in the environment."
futuresearch.ai/blog/litellm-p…
#genai #llms #litellm #infosec #python
Supply Chain Attack in litellm 1.82.8 on PyPI
litellm version 1.82.8 on PyPI contains a malicious .pth file that harvests SSH keys, cloud credentials, and secrets on every Python startup, then attempts lateral movement across Kubernetes clusters.Callum McMahon (FutureSearch)
TeamPCP injected malicious code into Trivy, Checkmarx tools, and LiteLLM in a supply chain attack designed to steal cloud credentials, tokens, and crypto wallet data.
Read: hackread.com/teampcp-trivy-che…
#CyberSecurity #Malware #TeamPCP #Trivy #Checkmarx #LiteLLM
TeamPCP Hits Trivy, Checkmarx, and LiteLLM in Credential Theft Campaign
Hackers compromised Trivy, Checkmarx, and LiteLLM in a supply chain attack, stealing cloud credentials, tokens, and crypto wallet data from developers.Deeba Ahmed (Hackread - Cybersecurity News, Data Breaches, AI and More)
Addressing the #LiteLLM supply chain incident:
All #SakuraSky managed production environments are unaffected by the v1.82.7/8 compromise.
Our infrastructure is a "Zero-Value Target." Using #OIDC and Just-in-Time key injection, we ensure that even if a library is breached, it finds an "empty room"- no static keys or .env files to steal.
We’re also accelerating our Sentinel framework for deeper AI agent governance.
Details: sakurasky.com/blog/security-ad…
#InfoSec #AI #SupplyChainSecurity #DevSecOps
Security Advisory: Resilience in the Face of the LiteLLM Supply Chain Incident
Sakura Sky confirms zero impact from the LiteLLM supply chain hack (v1.82.7/8). Learn how our 'Zero-Value Target' architecture and Sentinel framework protect managed AI environments.www.sakurasky.com


