Search
Items tagged with: exploit
#Windows #vulnerability reported by the #NSA exploited to install Russian #malware
When Microsoft patched the vulnerability in October 2022—at least two years after it came under #attack by the Russian hackers—the company made no mention that it was under active exploitation.
#patch #update #exploit #Russia #security #CyberSecurity #news #os #software #hack #hacker

Windows vulnerability reported by the NSA exploited to install Russian malware
Microsoft didn't disclose the in-the-wild exploits by Kremlin-backed group until now.Ars Technica
#CVE-2024-20356: #Jailbreaking a #Cisco appliance to run #DOOM
In this adventure, the Cisco #C195 device family was jailbroken in order to run unintended code. This includes the discovery of a vulnerability in the #CIMC body management controller which affects a range of different devices, whereby an authenticated high privilege user can obtain underlying root access to the server’s #BMC (CVE-2024-20356) which in itself has high-level access to various other components in the system. The end goal was to run DOOM – if a smart fridge can do it, why not Cisco?
source: https://labs.nettitude.com/blog/cve-2024-20356-jailbreaking-a-cisco-appliance-to-run-doom/
#software #security #bug #network #game #news #vulnerability #exploit #hack #hacker
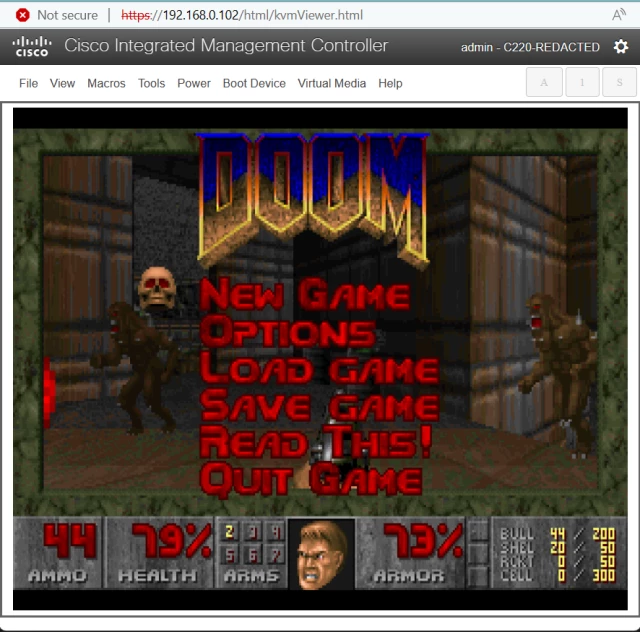
CVE-2024-20356: Jailbreaking a Cisco appliance to run DOOM - LRQA Nettitude Labs
Exploiting remote code execution in Cisco's CIMC management system and jailbreaking the device to run untrusted codeAaron Thacker (LRQA Nettitude Labs)
#LLM Agents can Autonomously #Exploit One-day Vulnerabilities
Source: https://arxiv.org/abs/2404.08144
To show this, we collected a dataset of 15 one-day vulnerabilities that include ones categorized as critical severity in the #CVE description. When given the CVE description, GPT-4 is capable of exploiting 87% of these vulnerabilities compared to 0% for every other model we test (GPT-3.5, open-source LLMs) and open-source vulnerability scanners (ZAP and #Metasploit).
#ai #technology #Software #chatgpt #bug #hack #news #cybersecurity

LLM Agents can Autonomously Exploit One-day Vulnerabilities
LLMs have becoming increasingly powerful, both in their benign and malicious uses. With the increase in capabilities, researchers have been increasingly interested in their ability to exploit cybersecurity vulnerabilities.arXiv.org

