Search
Items tagged with: infosec
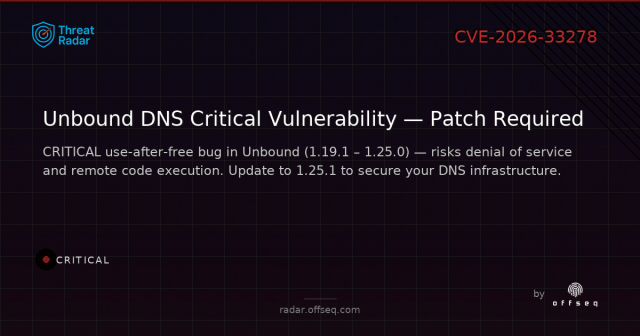
CVE-2026-33278: CWE-416: Use After Free in NLnet Labs Unbound
NLnet Labs Unbound 1.19.1 up to and including version 1.25.0 has a vulnerability in the DNSSEC validator that enables denial of service and possible remote code execution as a result of deep copying a data structure and erroneously overwriting a dest…OffSeq Threat Intelligence (OffSeq)
Today is L0pht Day. In 1998 7 hackers in suits told the US Senate the internet was a house of cards. We said we could take it down in 30 minutes. They looked at us like we'd landed from another planet.
28 yrs later, the gap between what the security community knows and what decision-makers act on remains a fundamental problem.
Miss you, Peter Neumann. He testified that day too, with decades of hard-earned wisdom. We owe him.
The work isn't done. It never was.
How does Fedora process patches for security vulnerabilities? The short answer is that we work to stay on top of the news to implement patches, working in the community and with Red Hat for updates.
The long answer: fedoramagazine.org/how-fedora-…
At the end of the day, the best thing you can do is keep your system updated. :)
#Fedora #Linux #Cybersecurity #InfoSec #OpenSource
How Fedora is responding to recent Kernel vulnerabilities - Fedora Magazine
Learn about the Fedora Project's process for managing package security vulnerabilities, in the context of recent Linux Kernel disclosures.Daniel Milnes (Fedora Project)
Local file exposure #vulnerability in linux kernels (CVE-2026-46333):
github.com/0xdeadbeefnetwork/s…
Apparently this issue was already identified in 2020 but wasn't fixed back then.
Mitigation:
- runtime:
sudo sysctl -w kernel.yama.ptrace_scope=2
- To make the mitigation persistent:
echo "kernel.yama.ptrace_scope=2" | sudo tee /etc/sysctl.d/01-harden-ptrace.conf
WARNING: This mitigation may break existing functionality. Test before deploying.
WARNING 2: While this mitigation does block the currently existing PoC, it may not prevent other attack vectors exploiting this vulnerability.
#infosec #cybersecurity #CVE_2026_46333

GitHub - 0xdeadbeefnetwork/ssh-keysign-pwn: Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels.
Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels. - 0xdeadbeefnetwork/ssh-keysign-pwnGitHub
Everybody hates #robocalls. But, despite tech reporting being willing to give the #FCC leeway, this new measure is not to stop robocalls, it won’t do a damn thing to stop robocalls. What it does is make burner phones illegal.
Burners are an integral part of many social justice actions. Protestors use them to record #ICE and other #cops. We include them in “Go Bags” to let abused women and children escape. They allow for anonymity.
They are a thorn in the side of the panopticon, and they are moving to eliminate them.
Stock up kids.
gizmodo.com/fcc-attempts-to-so…
wiley.law/alert-FCC-Proposes-S…
mashable.com/article/fcc-propo…
#burnerPhone #anon #infosec #privacy #palantir #gop #sjw
The FCC's proposed plan to fight spam calls puts consumer privacy in jeopardy
Burner phones might become a thing of the past if the FCC has its way.Phil Clark (Mashable)
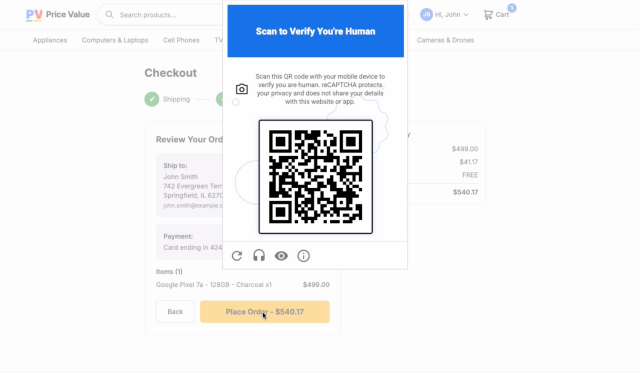
Well, the new Google ReCaptcha is awful, sheesh
It's a QR code you have to scan with a "proper" device - aka with Google Services installed
Goodbye last 10 years of phishing awareness, time to scan random QRs without a thought while you are purchasing things, woo! Seriously what were they thinking?
And because it's recommended to be put in "high risk" places, people will expect them to be seen there, and so a scam/phishing QR will be so much easier to slip in.
cloud.google.com/blog/products…
#google #captcha #recaptcha #phishing #infosec #cybersecurity
Introducing Google Cloud Fraud Defense, the next evolution of reCAPTCHA
Today at Next ‘26, we’re launching Google Cloud Fraud Defense, the trust platform for the agentic web and the next evolution of reCAPTCHA.Jian Zhen (Google Cloud)
Prompt Injection Attack Drains $155,000 from Grok-Linked Bankr Crypto Wallet
A prompt injection attack against xAI's Grok chatbot exploited the Bankr platform's social-feed command parser to steal $155,000 in cryptocurrency. The attacker bypassed security restrictions by airdropping an NFT to Grok's wallet and using Morse code to trick the AI into broadcasting a transfer command.
****
#cybersecurity #infosec #incident #theft
beyondmachines.net/event_detai…
Edit: issue seems fixed.
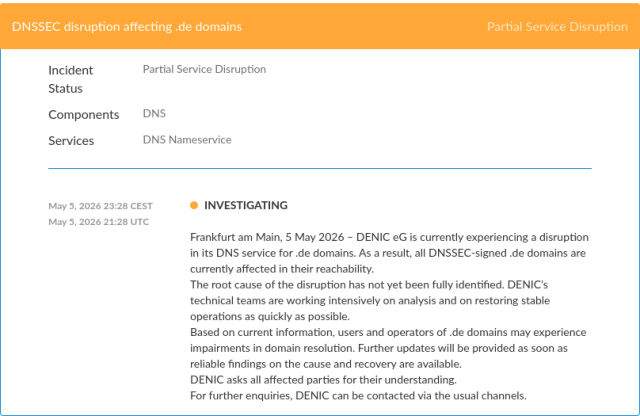
Looks like DE ccTLD is unresolvable due to DNSSEC issue:
dnsviz.net/d/nic.de/afpsNg/dns…
😬
🧵👇
RE: cyberplace.social/@GossiTheDog…
I HATE TO BE THAT GUY but even as this paints the security in a bad light… do we know if this wasn't aislopped?
we don’t.
and that's the point of #AI : it’s a complete rejection of The Social Contract on how we agree on the truth.
we need the #infosec community to help us create new, defensive fact checking protocols. the oligarchy wants to own reality, and define the truth. pushback on giving them the benefit of the doubt.
Y’ALL DID AND WE LOST THE RIGHT TO ABORTIONS, AND VOTING RIGHTS
Kevin Beaumont (@GossiTheDog@cyberplace.social)
If you're wondering how the gunman got past security at the Trump dinner event - there's a video in this article, he ran through the security checkpoint. It looks like an officer accidentally shoots another officer as he runs past them.Kevin Beaumont (Cyberplace)
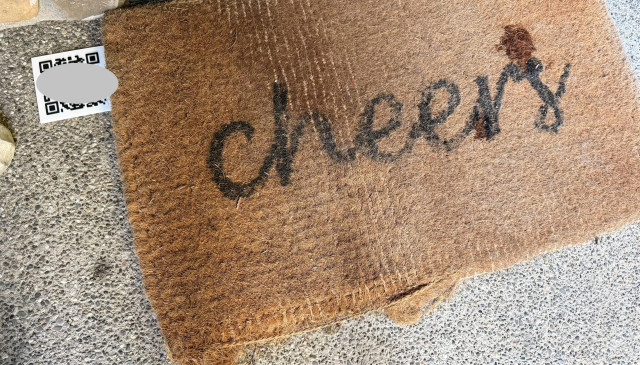
trying a new thing, have 3D printed a QR code and put it on the front porch
QR code triggers a canary token
want to see if any of the delivery companies are using the drop off proof of delivery pics to train AI
Copy Fail (CVE-2026-31431) has just been patched on Debian 13, with kernel version 6.12.85-1 from trixie (security).
A lot of people are apparently happily running a script clearly marked as a root exploit from some random website using curl | bash 
Some do inspect the script, but then still run it using curl | bash anyway. 
Incidentally, this very relevant blogpost about detecting curl | bash and serving different scripts based on that is almost exactly a decade old:
web.archive.org/web/2023031806…
Detecting the use of "curl | bash" server side | Application Security
Another reason not to pipe from curl to bash. Detecting curl | bash serverside.web.archive.org
#SCOTUS Reviews Police Use of #Cell #Location #Data to Find Criminals
#Geofence searches allow law enforcement to find suspects & witnesses by sweeping up #LocationData from cellphone users near crime scenes.
Geofence searches have become increasingly popular as a tool for law enforcement, but critics say they put at risk the personal data of everyday Americans & violate the #Constitution.
TUTORIAL: Switch Between Tor Browser Security Levels (without restarting browser)
Can even run all 3 security levels in separate windows (if wanted)
Normally switching levels means full browser restart / reconnect
Not having to restart browser means saving time, and not losing any tabs!
With ready to use desktop shortcuts.
#torbrowser #anonymous #anonymity #infosec #cybersecurity #Linux #FOSS #darknet #tornetwork #peertube