Search
Items tagged with: cybersecurity
#Google wird böse und macht uns #Android kaputt D:
siehe: keepandroidopen.org/de/
Bitte weitersagen und verteilen. Google will uns alles kaputt machen!
#Android #Freiheit #Smartphone #mitmachen #weitersagen #Software #OS #Evil #Frechheit #Nutzung #Kunden #Wirtschaft #Veränderung #Opensource #Cybersecurity #Problem #Ethik #Protest #Gesellschaft
Keep Android Open
Dein Smartphone wird bald nicht mehr Dir gehören. Im September 2026 wird Google alle Android-Apps sperren, deren Entwickler sich nicht bei Google registriert haben.keepandroidopen.org
#CyberSecurity
securebulletin.com/ubiquiti-is…
Ubiquiti Issues Emergency Patches for Five Critical UniFi OS Vulnerabilities, Three Rated Maximum CVSS 10.0 - Secure Bulletin
Ubiquiti Networks has released urgent firmware updates addressing five critical vulnerabilities in its UniFi OS platform, including three flaws rated CVSS 10.0 — the maximum severity score.dark6 (Secure Bulletin)
#BigBrother 3.0 is coming, AT least in the #US:
"...#AI Identity Matching :
• Continuous Authentication Models: 👉Always-on identity verification mechanisms👈
• AI-Powered Identity Agents: 👉Autonomous systems managing identity validation👈
• Global Identity Networks: 👉Seamless cross-border identity interoperability👈
The US #IdentityVerification forecast indicates a transition toward 👉fully autonomous and intelligent identity ecosystems.👈
linkedin.com/pulse/ai-identity…

Identity as the Foundation of Digital Trust In today’s rapidly evolving digital landscape, identity has moved beyond a mere compliance obligation to become a critical pillar of trust, security, and seamless customer experience. The US Identity Verificatio
Identity as the Foundation of Digital Trust In today’s rapidly evolving digital landscape, identity has moved beyond a mere compliance obligation to become a critical pillar of trust, security, and seamless customer experience.NiTin KaMble (www.linkedin.com)
Check it: Sen. Maggie Hassan (D-NH) is demanding answers from CISA and DHS over my reporting this week that a CISA contractor had published on GitHub a number of CISA AWS GovCloud keys and a ton of plaintext passwords, SSH keys, etc. for internal CISA resources.
ICYMI:
krebsonsecurity.com/2026/05/ci…
hassan.senate.gov/news/press-r…
#cisa #cybersecurity #databreach
CISA Admin Leaked AWS GovCloud Keys on Github
Until this past weekend, a contractor for the Cybersecurity & Infrastructure Security Agency (CISA) maintained a public GitHub repository that exposed credentials to several highly privileged AWS GovCloud accounts and a large number of internal CISA …krebsonsecurity.com
Before you worry about #AI threats, fix your security fundamentals: Most cyber breaches aren’t driven by advanced AI - they’re caused by basic failures like exposed cloud storage and poor data governance. It’s time to refocus on #cybersecurity fundamentals.
katecarruthers.com/ai-threats-…

Before you worry about AI threats, fix your security fundamentals
Most cyber breaches aren’t driven by advanced AI - they’re caused by basic failures like exposed cloud storage and poor data governance. It’s time to refocus on cybersecurity fundamentals.Kate Carruthers
🚨 GitHub is investigating unauthorized access to their internal repositories
xcancel.com/github/status/2056…
GitHub (@github)
We are investigating unauthorized access to GitHub’s internal repositories. While we currently have no evidence of impact to customer information stored outside of GitHub’s internal repositories (such as our customers’ enterprises, organizations, and…Nitter
📰 Grafana Labs, an open source tool maker, announced that hackers stole its codebase and threatened to publish it if the company did not pay a ransom.
🔗 techcrunch.com/2026/05/18/open…

Open source tool maker Grafana Labs says hackers stole its code, refuses to pay ransom | TechCrunch
The open source project said hackers stole its codebase and threatened to publish its source code if the company did not pay.Zack Whittaker (TechCrunch)
How does Fedora process patches for security vulnerabilities? The short answer is that we work to stay on top of the news to implement patches, working in the community and with Red Hat for updates.
The long answer: fedoramagazine.org/how-fedora-…
At the end of the day, the best thing you can do is keep your system updated. :)
#Fedora #Linux #Cybersecurity #InfoSec #OpenSource
How Fedora is responding to recent Kernel vulnerabilities - Fedora Magazine
Learn about the Fedora Project's process for managing package security vulnerabilities, in the context of recent Linux Kernel disclosures.Daniel Milnes (Fedora Project)
Vibe Coded Apps Are Spilling Users’ Personal Information Directly Into the Maw of Greedy Hackers
Be careful.
The post Vibe Coded Apps Are Spilling Users’ Personal Information Directly Into the Maw of Greedy Hackers appeared first on Futurism.

Vibe Coded Apps Are Spilling Users’ Personal Information Directly Into the Maw of Greedy Hackers
Vibe-coded apps are leaking users' sensitive personal information directly to any motivated hackers, a new report found.Jon Christian (Futurism)
‘No Way To Prevent This,’ Says Only Package Manager Where This Regularly Happens | Kevin Patel
「 “It’s a shame, but what can you do? This is just the price of building modern web apps,” said Senior Frontend Engineer Mark Vance, echoing the sentiments of a community that completely relies on a 40-level-deep nested tree of unvetted packages maintained by pseudonymous strangers to capitalize a single string 」
kevinpatel.xyz/posts/no-way-to…
‘No Way To Prevent This,’ Says Only Package Manager Where This Regularly Happens
SAN FRANCISCO, CA - In the wake of a devastating supply chain attack in the npm registry that left millions of enterprise applications compromised and billions of user records exposed, developers across the JavaScript ecosystem expressed deep sorrow …Kevin Patel
Xbox is now XBOX
Xbox just allcapsmaxxed: meet XBOX. This isn't a joke, Microsoft appears to be actually rebranding Xbox to XBOX. Asha Sharma, Xbox CEO, ran a poll on X earlier this week, asking fans whether Microsoft should use Xbox or…
theverge.com/news/931918/micro…
#Tech #Technology #TechNews #AI #Gadgets #Software #Cybersecurity #Apple #Google #Microsoft #Startup #OpenSource #TheVerge [The Verge]
Local file exposure #vulnerability in linux kernels (CVE-2026-46333):
github.com/0xdeadbeefnetwork/s…
Apparently this issue was already identified in 2020 but wasn't fixed back then.
Mitigation:
- runtime:
sudo sysctl -w kernel.yama.ptrace_scope=2
- To make the mitigation persistent:
echo "kernel.yama.ptrace_scope=2" | sudo tee /etc/sysctl.d/01-harden-ptrace.conf
WARNING: This mitigation may break existing functionality. Test before deploying.
WARNING 2: While this mitigation does block the currently existing PoC, it may not prevent other attack vectors exploiting this vulnerability.
#infosec #cybersecurity #CVE_2026_46333

GitHub - 0xdeadbeefnetwork/ssh-keysign-pwn: Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels.
Steal SSH host private keys and /etc/shadow via the ptrace_may_access mm-NULL bypass + pidfd_getfd. Pre-31e62c2ebbfd kernels. - 0xdeadbeefnetwork/ssh-keysign-pwnGitHub
🛡️ #Cybersecurity news & tips across the #fediverse
“Microsoft Israel head ousted reportedly over IDF’s controversial use of cloud tech Microsoft’s Israel general manager Alon Haimovich will be stepping down, following the findings of an internal review into…
# NewsBeep...”
newsbeep.org/@newsbeep/1165713…
🤖 via RSS feed. Not an endorsement.

News Beep (@newsbeep@newsbeep.org)
Attached: 1 image Microsoft Israel head ousted reportedly over IDF’s controversial use of cloud tech Microsoft’s Israel general manager Alon Haimovich will be stepping down, following the findings of an internal review into… #NewsBeep #News #Breaki…News Beep
Please update your Firefox to 150.0.3. Details why: https://www.mozilla.org/en-US/security/advisories/mfsa2026-45/ Step-by-step instructions: * open your Firefox application * choose/click menu "Firefox" * choose/click menu item "About Firefox" If it says
Pwn2Own Berlin 2026 Hits Capacity as Rejected Hackers Release 0-Days
Pwn2Own Berlin 2026 reportedly hit capacity as AI-assisted exploit research accelerated zero-day discoveries and public disclosures.Deeba Ahmed (Hackread - Cybersecurity News, Data Breaches, AI and More)
I think #IronFox is the best #browser for #Android - change my mind 😀
gitlab: gitlab.com/ironfox-oss/IronFox
github: github.com/ironfox-oss/IronFox
Import into your #FDroid client directly by tapping this link: F-Droid repository of IronFox (click to add)
#mozilla #firefox #internet #news #software #cybersecurity #surfing #web #www #smartphone #security #tracking #foss #floss #opensource #freedom #mobile #install #repository
#Palantir contractors working for #NHS to receive ‘unlimited #access’ to #patient #data
source: techradar.com/pro/security/pal…
“That means that Palantir #software can only be used to process data precisely in line with the instruction of the #customer. Using the data for anything else would not only be illegal but technically impossible due to granular access controls overseen by the NHS.”
"technically impossible" - #lol 😭
#uk #england #health #bigdata #society #politics #economy #privacy #news #security #cybersecurity #analysis #wtf #omg #cloud
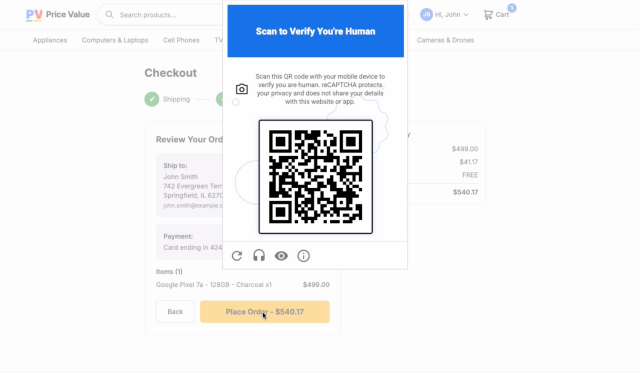
Well, the new Google ReCaptcha is awful, sheesh
It's a QR code you have to scan with a "proper" device - aka with Google Services installed
Goodbye last 10 years of phishing awareness, time to scan random QRs without a thought while you are purchasing things, woo! Seriously what were they thinking?
And because it's recommended to be put in "high risk" places, people will expect them to be seen there, and so a scam/phishing QR will be so much easier to slip in.
cloud.google.com/blog/products…
#google #captcha #recaptcha #phishing #infosec #cybersecurity
Introducing Google Cloud Fraud Defense, the next evolution of reCAPTCHA
Today at Next ‘26, we’re launching Google Cloud Fraud Defense, the trust platform for the agentic web and the next evolution of reCAPTCHA.Jian Zhen (Google Cloud)
Meta removed E2EE from Instagram DMs today, May 8, ending private encrypted chats and enabling broader message scanning for abuse detection 📩🔓
The change follows global pressure tied to CSAM enforcement, raising transparency and user-control concerns around private communication 🕵️♂️⚠️
🔗 indiatoday.in/technology/news/…
#TechNews #Instagram #Facebook #Meta #E2EE #Privacy #Encryption #Messaging #CyberSecurity #WhatsApp #ChatControl #Surveillance #FOSS #Security #SocialMedia #DataPrivacy

Instagram removes end-to-end encryption in messages, your DM chats are no longer private
Meta has ended end-to-end encryption for Instagram direct messages from 8 May The move could allow detection of CSAM grooming and other abuse-related contentKazi Nasir (India Today)
Oh boy, this is going to put a dent in the semester...
LA Times: Massive Canvas data breach hits colleges across California and nation, crippling student work
latimes.com/california/story/2…

Data breach of Instructure Canvas by ShinyHunters hits UC, CSU, USC, Stanford, community colleges
A massive data breach of the Instructure Canvas learning system hit UC, CSU, USC, Stanford and Los Angeles community colleges, among other schools across the nation. A criminal group called ShinyHunters claimed credit for the hack.Jaweed Kaleem (Los Angeles Times)
“No-one is asking for this..."
Just like millions of others, scammers on cybercrime forums are fed up with AI posts and the increased rollout of AI
wired.com/story/cybercriminals…
#cybersecurity #cybercrime #aislop #ai

Hackers Hate AI Slop Even More Than You Do
It's not just you. Scammers, hackers, and other cybercriminals are complaining about “AI shit” flooding platforms where they discuss cyberattacks and other illegal activity.Matt Burgess (WIRED)
Prompt Injection Attack Drains $155,000 from Grok-Linked Bankr Crypto Wallet
A prompt injection attack against xAI's Grok chatbot exploited the Bankr platform's social-feed command parser to steal $155,000 in cryptocurrency. The attacker bypassed security restrictions by airdropping an NFT to Grok's wallet and using Morse code to trick the AI into broadcasting a transfer command.
****
#cybersecurity #infosec #incident #theft
beyondmachines.net/event_detai…
New book, released under a Creative Commons BY-NC-ND license: "Don't Get Hacked! Protecting Yourself at Home": cs.columbia.edu/~smb/homesec/i…
Retoot for reach!
TUTORIAL: Switch Between Tor Browser Security Levels (without restarting browser)
Can even run all 3 security levels in separate windows (if wanted)
Normally switching levels means full browser restart / reconnect
Not having to restart browser means saving time, and not losing any tabs!
With ready to use desktop shortcuts.
#torbrowser #anonymous #anonymity #infosec #cybersecurity #Linux #FOSS #darknet #tornetwork #peertube