Search
Items tagged with: infoSec
#DarkWeb #Infosec #CTI #OSINT
#CEH #CPT #GPEN #Hacking #OSCP #snoopgodlinux #Ubuntu https://cybersecuritynews.com/hackers-abuse-windows-search/
Hackers Abuse Windows Search Functionality To Deploy Malware
Hackers use Windows Search's vulnerability to penetrate different layers and rooms in the client's systems and execute unauthorized code by using bugs in the search functionality itself.Tushar Subhra Dutta (CybersecurityNews)
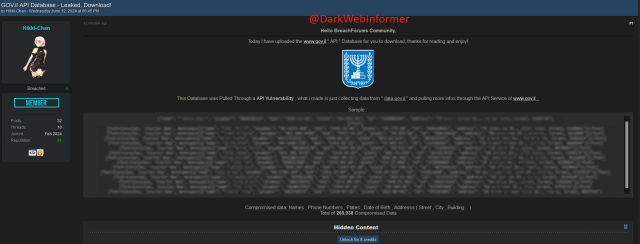
🚨DATA LEAK🚨A threat actor has allegedly leaked Israel's Government Services and Information API Database. 268,938 lines of data.
#DarkWeb #Cybersecurity #Security #Cyberattack #Cybercrime #Privacy #Infosec #Israel
Compromised Data includes: Names, Phone Numbers, Plates, DOB, Address.

Indiana cop who used Clearview AI facial recognition tech for personal reasons resigns
The Evansville Police Department officer was discovered to have used the controversial tool to search social media accounts.therecord.media
QR code SQL injection from popular biometric terminal
💥https://securelist.com/biometric-terminal-vulnerabilities/112800/
Nice blackbox analysis... *sigh* and yet another SQL injection in 2024.

QR code SQL injection and other vulnerabilities in a popular biometric terminal
The report analyzes the security properties of a popular biometric access control terminal made by ZKTeco and describes vulnerabilities found in it.Georgy Kiguradze (Kaspersky)
Excited that the team will be teaching 2 classes at @defcon in Vegas this summer: 1) Hunt Methodologies and 2) Advanced Tunneling, Pivoting, and Redirection. (Aug 12-13).
If those awesome topics alone aren't exciting enough, at the end of day 1 of trainings, the founder of #defcon, Jeff Moss will be hosting an evening social/mixer for trainers and students. More opportunities to grow your #infosec network - in person!
Hope to see you there!
Register for Hunt Meth here:
https://training.defcon.org/products/bobby-thomas-hunt-methodologies-dctlv2024
#threathunting
Register for Adv. Tunneling, Pivoting, and Redirection here:
https://training.defcon.org/products/travis-livermore-advanced-tunneling-pivoting-and-redirection-course-dctlv2024
#redteam #cybersecurity

Bobby Thomas - Hunt Methodologies - $2175
Trainer bio: Bobby Thomas has over 20 years of experience in cyber operations, network analysis, and exploitation.defcontrainings
I'll stick to #Bitwarden for the time being. @protonprivacy Pass has a long way to go. It lacks many basic features.
This dumb password rule is from Three.
Password must be at least 7 characters long.
The maximum length is inconsistent, however: when changing password, the maximum length is 30, but when resetting password via email link, the maximum length is 12.
https://dumbpasswordrules.com/sites/three/
#password #passwords #infosec #cybersecurity #dumbpasswordrules
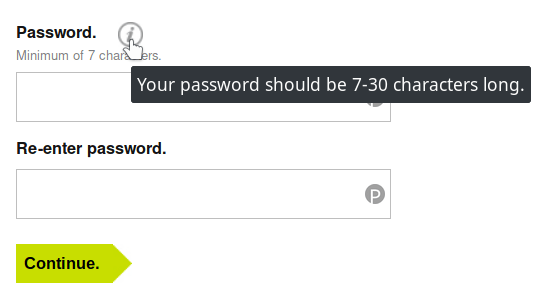
Three - Dumb Password Rules
Password must be at least 7 characters long. The maximum length is inconsistent, however: when changing password, the maximum length is 30, but when resetting password via email link, the maximum length is 12.dumbpasswordrules.com
Last year, CrowdStrike published a report on a new crypto-mining operation that was targeting exposed Kubernetes systems with a miner for the Dero cryptocurrency token.
This threat actor—no official name yet—is still active today, according to a new report from cloud security firm Wiz.
https://www.wiz.io/blog/dero-cryptojacking-campaign-adapts-to-evade-detection
#infosec #cybersecurity #security
Pause off my cluster: DERO cryptojacking takes a new shape
Learn how the threat actors behind the 2023 DERO cryptojacking campaign have adapted their techniques to evade detection, and the best practices for mitigation.Avigayil Mechtinger (Wiz.io)
I've done it! After literal months of work, I've finally finished my (rather long) blog post about how AES-GCM works and how it's security guarantees can be completely broken when a nonce is reused:
It includes more than 10 interactive widgets for you to try out AES-GCM, GHASH and the nonce reuse attack right in your browser! (Powered by #RustLang and #WASM )
If you're interested in #cryptography , #math (or #maths ) or #infosec you might find it interesting.
If you do read it, I'm all ears for feedback and criticism!
AES-GCM and breaking it on nonce reuse
In this post, we will look at how the security of the AES-GCM mode of operation can be completely compromised when a nonce is reused.frereit's blog
Lukewarm take:
When I see general* "security advice" that mentions "do not use public WiFi" or "use a VPN", I am immediately suspicious about all other advice offered.
Yes, a decade ago that was a consideration, because most sites were not using HTTPS. Credentials were flying cleartext on the wire.
Today, almost all sites use HTTPS. Doesn't mean the risk is zero, but it's way lower.
*) "general" meaning "without a very specific threat model in mind", meant for general public, etc.
Also, shout-out to @letsencrypt for dramatically changing the security landscape of the Web for the better over the years.
Rarely is there an example of a project so effective and so directly improving everyone's lives, while at the same time keeping the original engineering mindset and just Doing Stuff Right™ humbly in the background.
Next November it will have been exactly a decade since LE started. We all owe them a huge 10th birthday party.
Microsoft Recall: No admin necessary to access data…
#microsoft #recall #infosec #privacy
https://infosec.exchange/@tiraniddo/112566044174482506
James Forshaw :donor: (@tiraniddo@infosec.exchange)
Damn, I really thought the Recall database security would at least be, you know, secure. Turns out Microsoft did pretty much what I blogged about for WindowsApps, except you need to find a specific WIN://SYSAPPID instead.Infosec Exchange
#cybersecurity #hacking #Pentesting #DarkWeb #Infosec #CTI #OSINT #SnoopGod #SnoopGodLinux #Ubuntu https://www.securityweek.com/google-microsoft-russian-threat-actors-pose-high-risk-to-2024-paris-olympics/
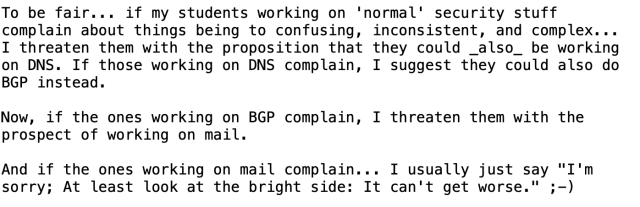
Seen on the MailOp list. A putative joke from Tobias Fiebig.
I’m not sure that I’d put BGP before mail in this hierarchy, but that's mostly because others around me handle it as well as can be expected in a world with the likes of Cogent and Tata swinging their dicks at each other.
#cybersecurity #hacking #Pentesting #DarkWeb #Infosec #CTI #OSINT #SnoopGod #SnoopGodLinux #Ubuntu https://www.wired.com/story/total-recall-windows-recall-ai/
#cybersecurity #infosec #advisory #vulnerability
https://beyondmachines.net/event_details/google-android-june-patch-fixes-a-total-of-37-flaws-v-7-4-m-w/gD2P6Ple2L

Google Android June patch fixes a total of 37 flaws
The Android Security Bulletin for June 2024 highlights several critical security vulnerabilities affecting various Android versions and components.BeyondMachines
STORY: Microsoft’s Recall AI system takes a screenshot of your laptop every five seconds. Even before it has launched, a security researcher has built a tool that can extract all the unencrypted data from Recall
https://www.wired.com/story/total-recall-windows-recall-ai/ #cybersecurity #infosec #technology #microsoft
#Windows #Recall demands an extraordinary level of #trust that #Microsoft hasn’t earned
This, as many users in #infosec communities on social media immediately pointed out, sounds like a potential #security #nightmare. That’s doubly true because Microsoft says that by default, Recall’s screenshots take no pains to redact sensitive information, from usernames and passwords to health care information to NSFW site visits. By default, on a #PC with 256GB of storage, Recall can store a couple dozen gigabytes of data across three months of PC usage, a huge amount of personal data.
#bigdata #privacy #bigbrother #cybersecurity #software #os #surveillance #danger #warning #AI #fail #news

Windows Recall demands an extraordinary level of trust that Microsoft hasn’t earned
Op-ed: The risks to Recall are way too high for security to be secondary.Ars Technica
#infosecjobs #hiring Alert: I'm hiring a career transition, entry-level, or intern-level web developer in Rust/Python at @redqueen.
We help managed service providers get and keep their small biz clients safe and secure!
This would be a great role for someone mid-career looking to move into a more technical role or into infosec, or who just finished a bootcamp or similar education.
Remote, US-only. Read the JD carefully or you'll miss the subject line requirement when you email me.
https://www.redqueendynamics.com/careers #cybersecurity #compliance #infosec

Careers | Red Queen Dynamics
Want to go down the rabbit hole of security with us? Join Red Queen in our journey to help Managed Service Providers protect their clients.Red Queen Dynamics

Stealing everything you’ve ever typed or viewed on your own Windows PC is now possible with two lines of code — inside the Copilot+ Recall disaster.
I wrote a piece recently about Copilot+ Recall, a new Microsoft Windows 11 feature which — in the words of Microsoft CEO Satya Nadella- takes “screenshots” of your PC constantly, and makes it into an…Kevin Beaumont (DoublePulsar)
#followfriday! Here's some #infosec / #cybersecurity accounts I've discovered from the past week to check out!
- @an00brektn
- @dieg0
Plus! Here's some folks from across the Fediverse who's instance names are awesome.
- @pointlessone
- @prettygood
- @markiplier
- @split
- @kopper
- @nev
- @z
- @president
- @EmilyK
All previous follow friday posts: https://shellsharks.com/notes/2023/10/20/infosec-mastodon-starter-pack#for-infosec-folks
Giant list of cool instance names (and those from said instances) here: https://shellsharks.com/notes/2024/03/29/the-whimsical-corners-of-the-fediverse
📡 HackRF Portapack H2 Audio RX App: Listening / Browsing / Shortwave / Radio
#HackRF #FOSS #tutorial #hardware #SDR #Portapack #MayhemFirmware #firmware #shortwave #radio #gadgets #tech #infosec #cyber #RX
https://tube.tchncs.de/w/4RNT554SNRULBimPFxSPfK

📡 Shortwave Listening: HackRF Portapack H2 Audio RX App
Discover New Radio Stations Using Portapack H2 Mayhem RX Audio App. Sharing Tips For Getting Started Browsing For Shortwave Stations Using Audio RX Receive Application; We Start By Practicing With ...tchncs
Ticketmaster hacked. Breach affects more than ***half a billion*** users.
Emails, phone numbers, addresses, and even financial details have allegedly been exposed by a notorious hacker group. And they are offering the data for half a million bucks.
https://mashable.com/article/ticketmaster-data-breach-shinyhunters-hack
@404mediaco exposed Ticketmaster yesterday for its monopoly power in the concert industry, so its 500 million customers are now being revictimized by the hackers.
https://www.404media.co/the-monopoly-case-against-ticketmaster-explained/

The Monopoly Case Against Ticketmaster, Explained
The antitrust suit against Live Nation is not about ticket scalping or ticket sales. It's about total domination over the entire concert industry.Jason Koebler (404 Media)
STORY: Police have a new cybercrime fighting tactic: getting into the heads of Russian hackers.
Recent law enforcement takedowns of cybercrime groups have increasingly used psychological tactics as part of their disruption.
https://www.wired.com/story/cop-cybercriminal-hacker-psyops/
#cybersecurity #hacking #Pentesting #DarkWeb #Infosec #CTI #OSINT #SnoopGod #SnoopGodLinux #Ubuntu https://thehackernews.com/2024/05/indian-national-pleads-guilty-to-37.html?m=1
"I'm going to #DEFCON32 this year. Maybe I should enter one of the contests, that should test my expensive #cybersecurity skills and winning will advance my #infosec career!"
The Contests At @defcon:
Kyivstar Cyberattack: Company Allocates $90 Million for Recovery Efforts
The Kyivstar cyberattack fallout requires $90 million in recovery efforts. Insights on impacts and cybersecurity measures.Ashish Khaitan (The Cyber Express)
#nahamsec is still going strong!
Watch on the #DCG201 LIVE STREAM or on these direct links:
#Twitch: https://twitch.tv/namhamsec
#YouTube: https://www.youtube.com/live/76mNNVVBht0
NEW: second judge in #Poland reportedly confirmed as #Pegasus spyware victim.
Appeals court judge told reporter her responsibilities included classified cases where wiretapping was used.
Poland's spyware reckoning continues.
[PL, machine trans.]
Story: https://oko.press/wiemy-o-drugim-polskim-sedzi-inwigilowanym-pegasusem-to-sedzia-apelacyjna-z-krakowa-news-oko-press
#spyware #infosec #cybersecurity #polska #malware #security #intelligence #surveillance
Wiemy o drugim polskim sędzi inwigilowanym Pegasusem. To sędzia apelacyjna z Krakowa [News OKO.press]
Nie tylko sędzia Beata Morawiec, prezeska Themis, była za władzy PiS inwigilowana Pegasusem. Służby specjalne szpiegowskiego oprogramowania użyły też przeciwko krakowskiej sędzi apelacyjnej Beacie Barylak-PietrzkowskiejMariusz Jałoszewski (OKO.press)
#cybersecurity #hacking #Pentesting #DarkWeb #Infosec #CTI #OSINT #SnoopGod #SnoopGodLinux #Ubuntu https://thehackernews.com/2024/05/fake-antivirus-websites-deliver-malware.html?m=1
#cybersecurity #hacking #Pentesting #DarkWeb #Infosec #CTI #OSINT #SnoopGod #SnoopGodLinux #Ubuntu https://thehackernews.com/2024/05/researchers-warn-of-chinese-aligned.html?m=1

Homeland Security has collected DNA data from 1.5 million immigrants in four years, researchers find
Since a Trump administration rule mandating the collection of all detained immigrants’ DNA went into effect in 2020, the number of collected DNA profiles has shot up 50-fold.therecord.media