Search
Items tagged with: Security
The attribution for Mastodon's CVE-2026-46349 (CVSS 5.3, retracted boost reissuance) is interestingly reported as:
"This security issue has been reported by Doyensec in collaboration with Claude and Anthropic Research"
Is this how they say "Mythos" without revealing that Doyensec is one of the undisclosed Project Glasswing members?
github.com/mastodon/mastodon/s…
w.on-t.work/activitypub/may-20… says:
"Doyensec has contacted us on *behalf* of Anthropic".
#security #mastoadmin #mythos #ai #glasswing
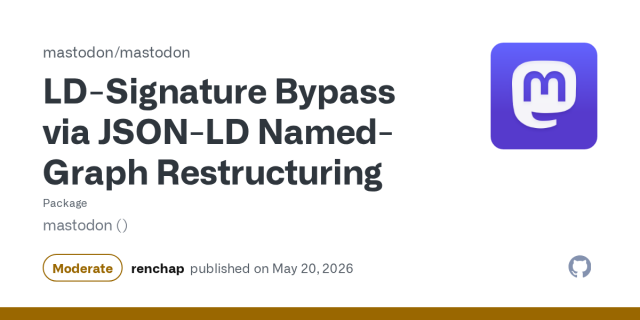
LD-Signature Bypass via JSON-LD Named-Graph Restructuring
### Summary Mastodon's normalization of incoming activities signed with Linked-Data Signatures does not sufficiently protect the activities from a certain class of spoofing, allowing attackers t...GitHub
The GitHub Breach Through VS Code Is the One I Warned About
The GitHub Breach Through VS Code Is the One I Warned About
GitHub confirmed unauthorized access through a malicious VS Code extension — an attack surface I presented at Black Hat MEA last December. Here's how I see it.Mazin Ahmed
and folks in this thread: At the risk of feeding myself to the lions, may I suggest care? Gutmann's views on QC are funny to watch, but prone to misinterpretation (although I have to say, this slide in particular is... refreshingly sober?)
gagliardoni.net/#20250714_ludd…
#security #cryptography #crypto #qc #quantum #quantumcomputing #drama
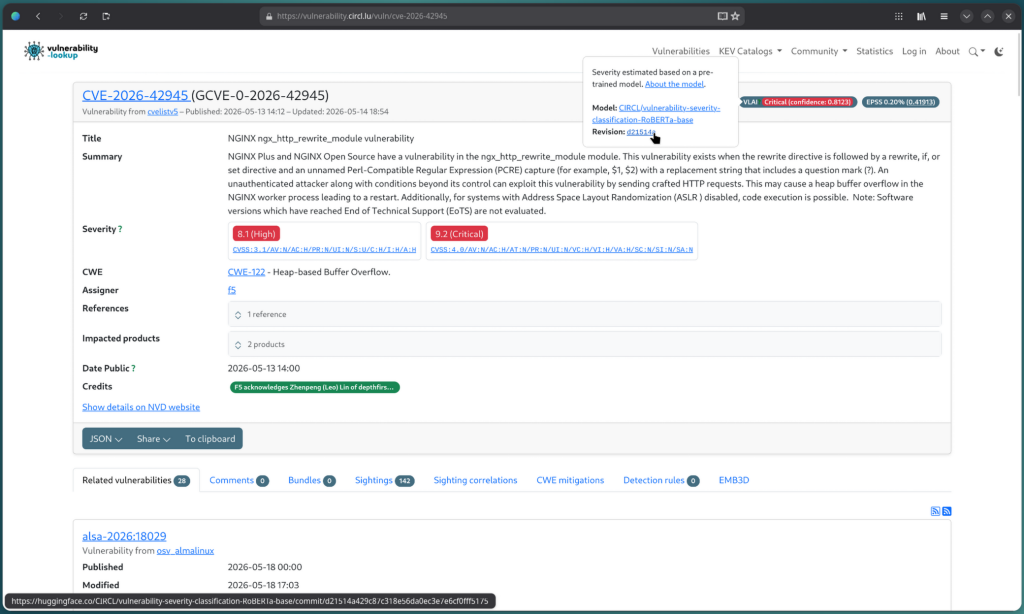
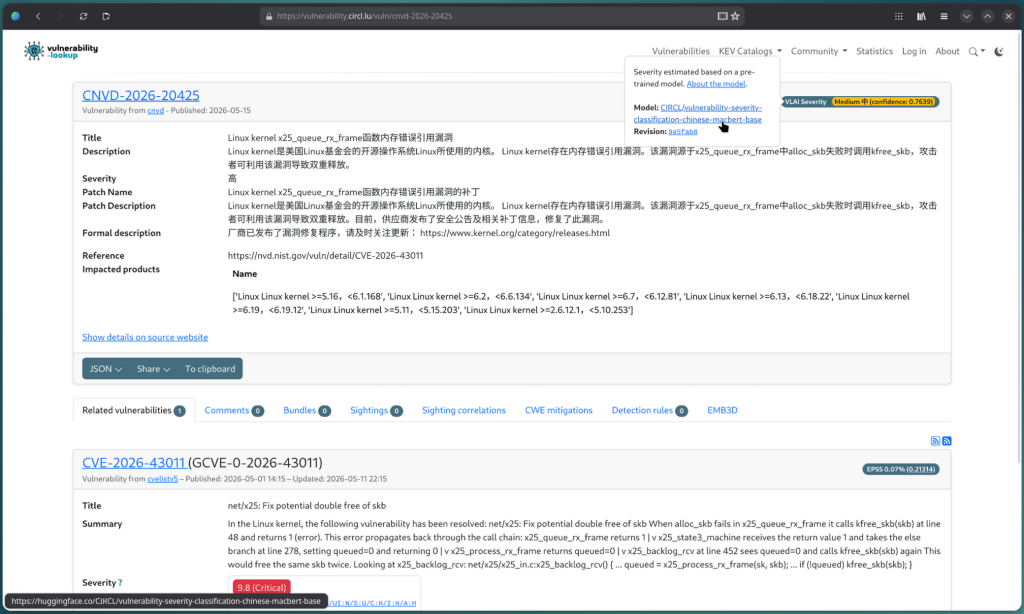
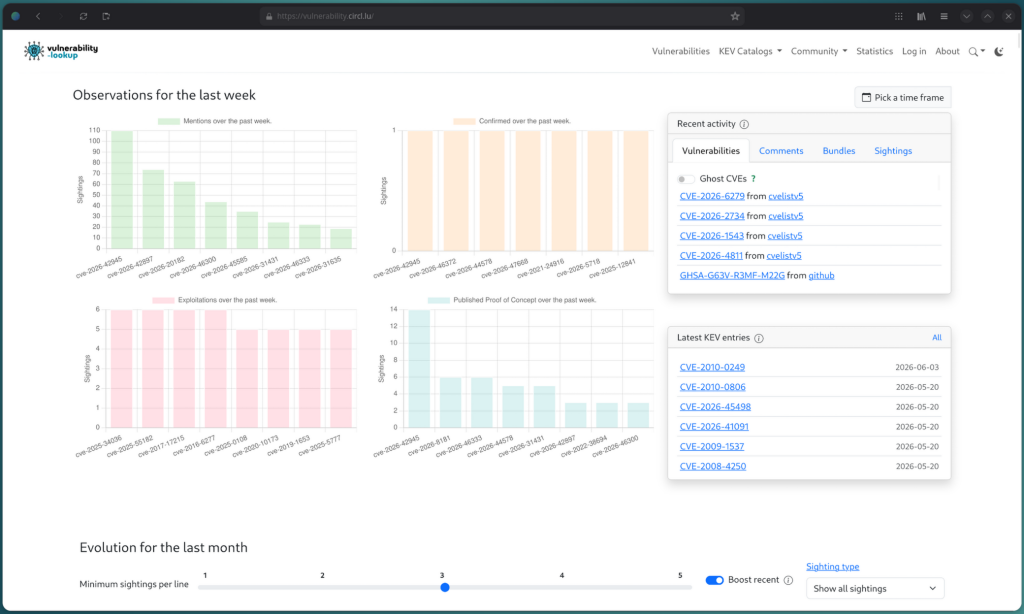
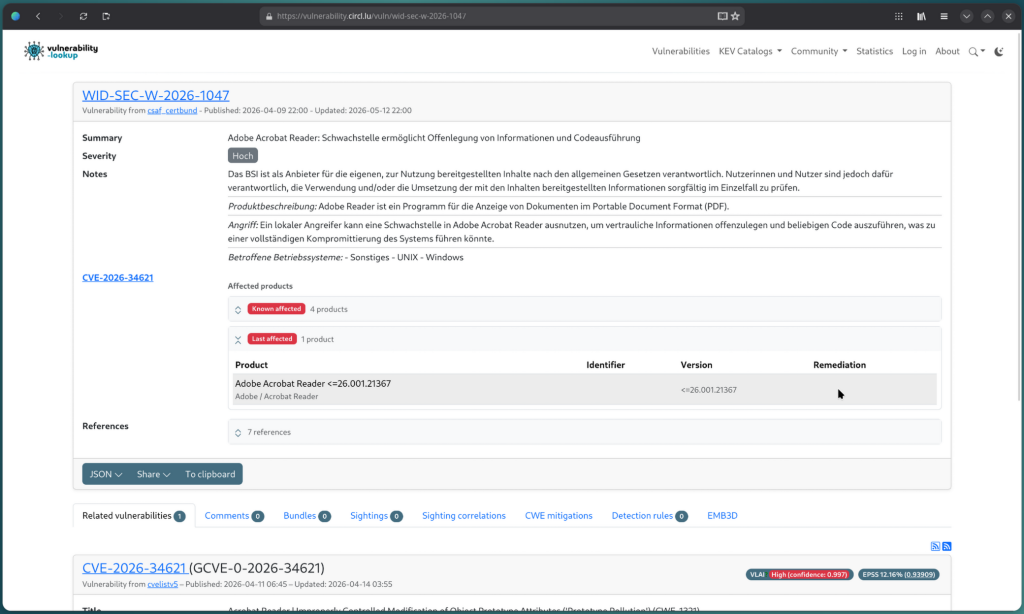
Vulnerability-Lookup 4.6.0
VLAI: A RoBERTa-Based Model for Automated Vulnerability Severity Classification
This paper presents VLAI, a transformer-based model that predicts software vulnerability severity levels directly from text descriptions.arXiv.org
ESA and Spain strengthen ties for secure connectivity

ESA and Spain strengthen ties for secure connectivity
The European Space Agency (ESA) and the Agencia Espacial Española (AEE) signed a Memorandum of Intent on 20 May to strengthen cooperation on secure satellite connectivity, reinforcing Spain’s growing strategic role in Europe’s space and resilience am…www.esa.int
RE: techhub.social/@Techmeme/11660…
Remember this whenever you hear claims that your data is secure on some system or other that you do not own and control.
Like all that additional data governments want to gather via the slippery slope of “age verification” in the EU.
The only data that is actually secure on a third party is data you haven’t shared with the third party.
Hence: data minimisation.
Had I mentioned GDMR yet today? Because I feel I might have. But hey, here it is again:
ar.al/2018/11/29/gdmr-this-one…
#data #security #privacy #GDMR #microsoft #github #hack

GDMR: this one simple regulation could end surveillance capitalism in the EU
GDMR: The regulation EU citizens deserve. No, you didn’t misread it and, no, it’s not a typo. GDMR – the General Data Minimisation Regulation – can end surveillance capitalism in the EU. The problem is that no such regulation exists.Aral Balkan
"Age verification is an impossibility, and an impossibly terrible idea with impossibly vast consequences for privacy and the open web..." - @pluralistic
twitter.com/github/status/2056… #GitHub #InternetSafety #DataBreach #HackerNews #ngated
(Nitter addon enabled: Twitter links via https://nitter.privacytools.io)
Hidden Voice Glitches Could Hijack Audio AI Tools
Hidden Signals Can Hijack AI Voice Systems
Research shows sounds unheard by human ears can hijack models’ behaviorEdd Gent (IEEE Spectrum)
CISA Admin Leaked AWS GovCloud Keys on Github
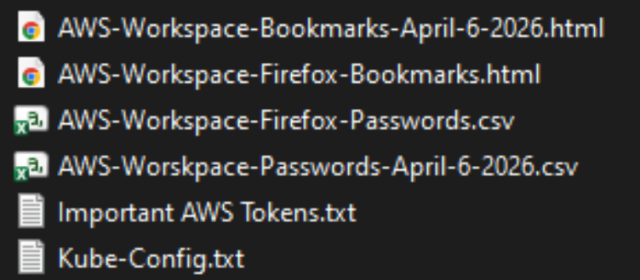
CISA Admin Leaked AWS GovCloud Keys on Github
Until this past weekend, a contractor for the Cybersecurity & Infrastructure Security Agency (CISA) maintained a public GitHub repository that exposed credentials to several highly privileged AWS GovCloud accounts and a large number of internal CISA …krebsonsecurity.com
RE: mamot.fr/@pluralistic/11660022…
I'm inclined to think @pluralistic has had entirely enough of this bullshit & so should we all...
Fabricked: Misconfiguring Infinity Fabric to Break AMD SEV-SNP (software-based compromise of "Confidential Virtual Machines")
confidential virtual machines aren't confidential?
cross-posted from: lemmy.bestiver.se/post/1112223
Comments
Thanks to AI, hackers quickly discovered new vulnerabilities such as CopyFail, DirtyFrag, and Fragnesia. They use LLMs to analyse Linux, finding and exploiting the security flaws faster than ever. The expertise required to hack is at an all-time low.
The Fedora Project decided to explain which precautions are being put in place to protect your system:
🌍 fedoramagazine.org/how-fedora-…
#security #opensource #foss #linux #kernel #fedora #redhat #hacking #ai #llm #coding #copyfail #dirtyflag #fragnesia
How Fedora is responding to recent Kernel vulnerabilities - Fedora Magazine
Learn about the Fedora Project's process for managing package security vulnerabilities, in the context of recent Linux Kernel disclosures.Daniel Milnes (Fedora Project)
PSA: open source security considerations in the era of LLMs
security tweaks · 093a466935
pyfedi - Project background: https://join.piefed.social. Flagship instance: https://piefed.socialCodeberg.org
A 0-click exploit chain for the Pixel 10: When a Door Closes, a Window Opens

A 0-click exploit chain for the Pixel 10: When a Door Closes, a Window Opens
We recently published an exploit chain for the Google Pixel 9 that demonstrated it was possible t...projectzero.google
Data Poisoning: The Fatal Flaw in Mass Surveillance
How to use data poisoning to trick the algorithm that’s profiling you (and why “personalization” is more fragile than you think)
youtu.be/AJf4SNuDnoI?si=lUk9FD…
Note: For education and defensive awareness only. I’m explaining the concept of data poisoning so teams can recognize risks and build safer systems. I’m not encouraging or providing guidance for misuse. :)
#DataPoisoning #AI #Algorithms #DataMining #DataPrivacy #Security
Internet of #Shit: #AI #Poop Analysis App Offered to Sell Me Database of Its Users' Poops
#privacy #security
404media.co/ai-poop-analysis-a…
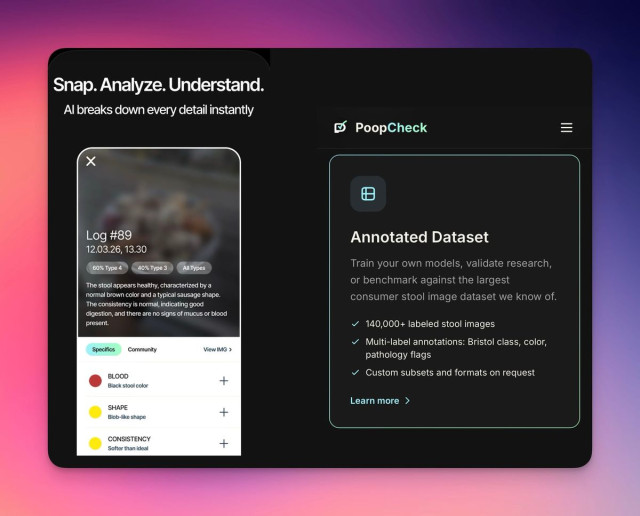
Internet of Shit: AI Poop Analysis App Offered to Sell Me Database of Its Users' Poops
"I hoarded a large database of something valuable, just not what you expect… 150k stools images."Jason Koebler (404 Media)
Please update your Firefox to 150.0.3. Details why: https://www.mozilla.org/en-US/security/advisories/mfsa2026-45/ Step-by-step instructions: * open your Firefox application * choose/click menu "Firefox" * choose/click menu item "About Firefox" If it says
Pwn2Own Berlin 2026 Hits Capacity as Rejected Hackers Release 0-Days
Pwn2Own Berlin 2026 reportedly hit capacity as AI-assisted exploit research accelerated zero-day discoveries and public disclosures.Deeba Ahmed (Hackread - Cybersecurity News, Data Breaches, AI and More)
A worm just ate its way through the NPM registry...
- YouTube
Bekijk je favoriete video's, luister naar de muziek die je leuk vindt, upload originele content en deel alles met vrienden, familie en anderen op YouTube.www.youtube.com
Counterterrorism Czar’s Blueprint Targets Leftists, Ignores Far-Right Violence and Heaps Praise on Trump
---
Sebastian Gorka’s anti-terror plan makes no mention of long-established threats posed by far-right militants and instead villainizes the president’s political enemies. “This administration is not paying attention to the data,” one expert said.
propublica.org/article/trump-c…
#News #Terrorism #Trump #USPolitics #Violence #Security #Extremism
France investigates 15-year-old over alleged hack of national ID agency

Hackers Claim 19M Records Stolen From French Government Agency
The France Titres discovered a security incident.Security Staff (www.securitymagazine.com)
I think #IronFox is the best #browser for #Android - change my mind 😀
gitlab: gitlab.com/ironfox-oss/IronFox
github: github.com/ironfox-oss/IronFox
Import into your #FDroid client directly by tapping this link: F-Droid repository of IronFox (click to add)
#mozilla #firefox #internet #news #software #cybersecurity #surfing #web #www #smartphone #security #tracking #foss #floss #opensource #freedom #mobile #install #repository
#Palantir contractors working for #NHS to receive ‘unlimited #access’ to #patient #data
source: techradar.com/pro/security/pal…
“That means that Palantir #software can only be used to process data precisely in line with the instruction of the #customer. Using the data for anything else would not only be illegal but technically impossible due to granular access controls overseen by the NHS.”
"technically impossible" - #lol 😭
#uk #england #health #bigdata #society #politics #economy #privacy #news #security #cybersecurity #analysis #wtf #omg #cloud
Meta removed E2EE from Instagram DMs today, May 8, ending private encrypted chats and enabling broader message scanning for abuse detection 📩🔓
The change follows global pressure tied to CSAM enforcement, raising transparency and user-control concerns around private communication 🕵️♂️⚠️
🔗 indiatoday.in/technology/news/…
#TechNews #Instagram #Facebook #Meta #E2EE #Privacy #Encryption #Messaging #CyberSecurity #WhatsApp #ChatControl #Surveillance #FOSS #Security #SocialMedia #DataPrivacy

Instagram removes end-to-end encryption in messages, your DM chats are no longer private
Meta has ended end-to-end encryption for Instagram direct messages from 8 May The move could allow detection of CSAM grooming and other abuse-related contentKazi Nasir (India Today)
Linux Dirtyfrag vulnerability
GitHub - V4bel/dirtyfrag
Contribute to V4bel/dirtyfrag development by creating an account on GitHub.GitHub
DAEMON Tools software infected – supply chain attack ongoing since April 8, 2026

Popular DAEMON Tools software compromised
Targeted by threat actors: individuals and organizations across 100+ countries and territories, with the majority of victims located in Russia, Brazil, Turkey, Spain, Germany, France, Italy, and China.Securelist
#Canadian #election databases use "canary traps"—and they work
In a world awash in high-tech #security tools like #passkeys , quantum-safe algorithms, & public-key #cryptography , it can be refreshing to get back to the simple things... like a good old-fashioned #canary trap.
The canary trap is a simple tool often used to identify #leakers or #doubleagents. To make one, you simply share a document, image, or DB but make tiny changes that are unique to each recipient.
arstechnica.com/tech-policy/20…

Canadian election databases use "canary traps"—and they work
Intentional errors can be useful.Nate Anderson (Ars Technica)
#GOP offers a ridiculous additional $1B for #WhiteHouse “security”, sparking dispute over #ballroom
#Senate #Republicans maintain their proposal would authorize #security construction, but not the #Trump ballroom. The White House disagrees.
Senate Republicans late Monday proposed $1 billion to pay for new White House security measures, with lawmakers & White House ofcls disagreeing over whether the #legislation would cover Trump’s planned ballroom.
Microsoft Edge: Passwords end up in memory as plaintext

Microsoft Edge: Passwords end up in memory as plaintext
The Edge password manager appears secure: encrypted storage, secured by Windows Hello. But plaintext is stored in memory.Dirk Knop (heise online)
I Reached Out to the White House Counterterrorism Czar for Comment. He Lashed Out on X.
---
Sebastian Gorka accused a ProPublica reporter of writing a “putrid piece of hackery” about him. Here’s how basic beat reporting led to a broader story about the state of the U.S. counterterrorism mission at a critical moment.
propublica.org/article/sebasti…
#News #WhiteHouse #Government #USPolitics #Security #Journalism
Vulnerability Report - April 2026

VLAI: A RoBERTa-Based Model for Automated Vulnerability Severity Classification
This paper presents VLAI, a transformer-based model that predicts software vulnerability severity levels directly from text descriptions.arXiv.org
Your face is becoming your password, and you can’t change your face.
Facial recognition systems turn your identity into a permanent digital key. If that data is breached, it’s not just another hack — it’s a lifelong vulnerability that can track you, expose you and be nearly impossible to undo.
theconversation.com/facial-rec…
theconversation.com/facial-rec…
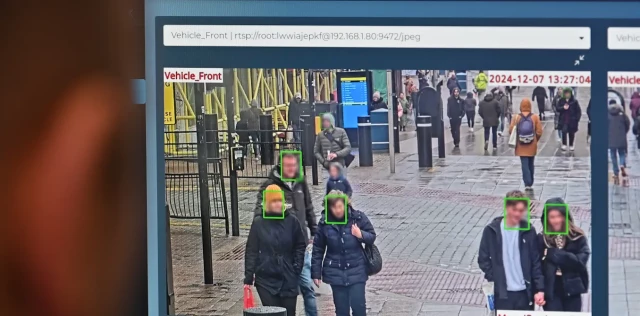
Facial recognition data is a key to your identity – if stolen, you can’t just change the locks
You can change a stolen password or credit card, but you can’t reset your face when your biometric data is breached.The Conversation
Copy Fail — 732 Bytes to Root

Copy Fail — 732 Bytes to Root
CVE-2026-31431. 100% Reliable Linux LPE — no race, no per-distro offsets, page-cache write that bypasses on-disk file-integrity tools and crosses containers. Found by Xint Code.Xint
Officer shot in bullet-resistant vest at correspondents’ dinner but is expected to be OK, law enforcement official says
The #FBI said the shooter is in & and that its Washington field office is responding to the #shooting.
The suspect is alive & has been transported to a hospital, according to one US official & one law enforcement official.
A #SecretService agent was injured & is in the hospital, a US official said.
#Trump said that a “shooter has been apprehended” in a post to Truth Social about 30 minutes following a security incident at the White House correspondents’ dinner.
Both Trump & JD #Vance were uninjured in the incident.
Trump to give statement at White House after #shooting incident at correspondents’ dinner