Search
Items tagged with: cyberSecurity
STORY: Thousands of listings on Eventbrite have been pushing people towards buying Gmail, Stripe accounts; escort services in India; and illegal sales of prescription drugs like Xanax, Valium, and oxycodone.
We found sales of opioids were pushed alongside events promoting drug addiction recovery and treatment. Eventbrite has investigated and says the “identified illegal and illicit activity has been removed.”
https://www.wired.com/story/sex-drugs-and-eventbrite/ #news #tech #cybercrime #cybersecurity
How to protect your #privacy with an SBC-powered #VPN #server
source: https://www.xda-developers.com/set-up-vpn-server-on-sbc/
Virtual Private Networks (VPNs) are an effective means to enhance your privacy. By disguising your IP address, a VPN prevents third-parties from tracking your #online activities on top of protecting your data from network-based hacking attacks.
#news #cybersecurity #opensource #network #internet #security

How to protect your privacy with an SBC-powered VPN server
A PiVPN server is the best way to protect your privacy without exposing your data to a third-party VPN providerAyush Pande (XDA)
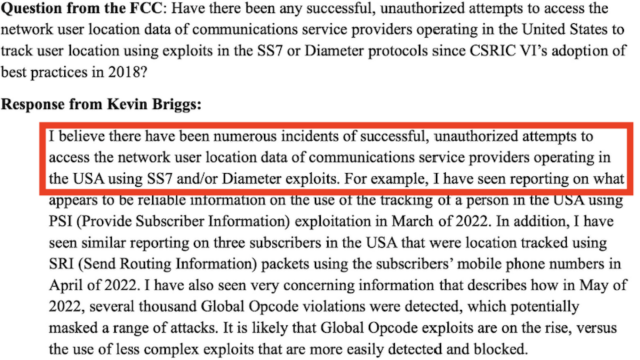
FINALLY: a 🇺🇸US official speaks the truth security researchers keep warning about...
Americans' movements being tracked with well-known weaknesses that US telcos aren't fixing.
It's remarkable how bad the problem with #SS7 & #Diameter is.
Must-read story by @josephcox
https://www.404media.co/cyber-official-speaks-out-reveals-mobile-network-attacks-in-u-s/
#infosec #cybersecurity #hacking #intelligence #surveillance #espionage
Cyber Official Speaks Out, Reveals Mobile Network Attacks in U.S.
A CISA official breaks with the government narrative and tells the FCC that SS7 and similar networks and protocols have been used to track people in the U.S. in recent years.Joseph Cox (404 Media)
An open-source hacking #hardware platform based on the #RP2040 with #RF, #NFC, #USB, and #SD card ready for pen testing #research.
source: https://www.hackster.io/pablotrujillojuan/hackbat-1dfdbc
In the #cybersecurity field, engineers are always looking for vulnerabilities in order to fix them and prevent other actors could taking advantage of them. The tools used by these engineers can be expensive and, on many occasions, the tools don't fit exactly with the requirements that engineers need. In this project, I want to present an open-source hardware platform with some tools used in cybersecurity, especially in pen testing. The board is named Hackbat and features an RF transceiver, NFC communication, SD card, USB, and #WIFI. All of this is managed by the #RaspberryPI #microcontroller RP2040. The schematic and the PCB design are open-source and are available on GitHub. Let's take a part-by-part look at the #Hackbat.
#news #opensource #tool #pentest

Hackbat
An open-source hacking hardware platform based on the RP2040 with RF, NFC, USB, and SD card ready for pen testing research.Hackster.io

Risky Biz News: Feds seize BreachForums again
In other news: The Netherlands criminalizes cyber-espionage; US arrests woman running laptop farm for DPRK IT workers; major hack at Australian healthcare org.Catalin Cimpanu (Risky.Biz)
Purchased This Random X13 "Bug Detector" Demo "Signal Detection" Mode On Channel
Watch To See Demo Using HackRF Portapack H2 + Baofeng + Fan Remote
#Infosec #privacy #cybersecurity #hackrf #portapack #surveillance #HumanRights #X13 #baofeng #sdr #radio
https://tube.tchncs.de/w/uts6e3bEhGFLn6XBHzWaQf
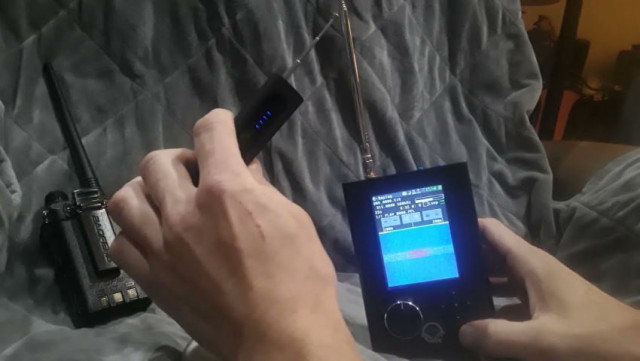
X13 RF Signal Detection Demo: #HackRF #Portapack / #Baofeng /
Testing RF Signal Detection On X13 affordable bug detector device, sold on the internet. We use a baofeng, wireless remote, and HackRF + Portapack to test the sensitivity on the X13. This one claim...tchncs
This is intended for store shelves to inform customers before they buy. And hopefully, it will spur negligent manufacturers to do better. #cybersecurity #infosec
White House: Cyber trust label could be in place by end of the year https://therecord.media/cyber-trust-label-coming-this-year @therecord_media

Cyber trust label could be in place by end of the year, White House says
The Biden administration hopes to have consumer devices that have been approved by a voluntary cybersecurity labeling program on store shelves soon.therecord.media
New Tor Browser Download With Firefox Security Updates
#Tor #privacy #anonymous #infosec #cybersecurity #Firefox
https://blog.torproject.org/new-release-tor-browser-13015/

New Release: Tor Browser 13.0.15 | Tor Project
Tor Browser 13.0.15 is now available from the Tor Browser download page and also from our distribution directory.blog.torproject.org
Why is #Mozilla collecting our #search data?
source: https://blog.mozilla.org/en/products/firefox/firefox-search-update/
Sensitive topics, like searching for particular health care services, are categorized only under broad terms like health or society. Your search activities are handled with the same level of confidentiality as all other data regardless of any local laws surrounding certain health services.
Hello Mozilla, I use Firefox because my privacy is important to me. The best security is still achieved if you don't collect the data. That is why I will use a fork that does not collect search data. It would be nice if Mozilla took user privacy more seriously.
#privacy #news #browser #web #internet #firefox #security #cybersecurity #surveillance #statistics #bigdata #bigbrother

See what’s changing in Firefox: Better insights, same privacy
We’re ramping up our efforts to enhance search experience by developing new features like Firefox Suggestions.Mozilla (The Mozilla Blog)
Apparently Google accidentally deleted all online data from UniSuper, a superannuation fund with half a million members.
UniSuper was only able to restore from backups from a different service. If they'd been solely relying on Google, then UniSuper and their members would be screwed.
Google says "This is an isolated, ‘one-of-a-kind occurrence’" But I'm seeing reports on Lemmy claiming to have dealt with similar problems with Google, suggesting this only the first *major* customer it has happened to.
In any case, don't put all your eggs in one basket. Even that that basket tries to make it ever-so-convenient for you to give them everything.
#google #cybersecurity #unisuper

Google Cloud accidentally deletes UniSuper’s online account due to ‘unprecedented misconfiguration’
Super fund boss and Google Cloud global CEO issue joint statement apologising for ‘extremely frustrating and disappointing’ outageJosh Taylor (The Guardian)
Do you want to learn how to setup an air-gapped #Nextcloud for maximum privacy and data protection?
Join me on May 22nd at 9 am EDT / 3 pm CEST on a free webinar to learn about air-gapped Nextcloud:
🔍 Critical factors to consider
🛡️ Four customizable air-gapped setups
🔧 Setting up air-gapped Nextcloud instances
💼 Best practices for Nextcloud maintenance
Register for free:
https://bit.ly/3QB2dlv
#OpenSource #GovTech #Security #CyberSecurity #infosec #privacy #sysadmin #datasecurity
![[Webinar] Beyond Secure: Air-gapped Nextcloud for highly confidential data](https://friendica.hellquist.eu/photo/preview/640/2662225)
[Webinar] Beyond Secure: Air-gapped Nextcloud for highly confidential data
Join us to learn how you can set up air-gapped Nextcloud for highly confidential data ideal for military, government, and large enterprises.Nextcloud
The conflict between Israel and Hamas is happening online as well as on the ground – with phishing attacks and hacking efforts targeting civilians on both sides.
https://theconversation.com/a-look-inside-the-cyberwar-between-israel-and-hamas-reveals-the-civilian-toll-228847
#Israel #Hamas #Technology #Cybersecurity

A look inside the cyberwar between Israel and Hamas reveals the civilian toll
The consequences of cyber conflict are primarily felt by civilians, who call for retaliation, fueling cycles of violence.The Conversation
I'll give this a shot.
I'm looking to #GetFediHired for a role in #cybersecurity. I've done both offensive (see e.g. https://github.com/qwell/disclosures/) and defensive security work, and have over 20 years of software development experience in many different languages.
ISC2 CC
DMs always open.
#FediHire #FediHired (we should pick a hashtag and stick with it) #InfoSec

GitHub - qwell/disclosures: List of vulnerability disclosures
List of vulnerability disclosures. Contribute to qwell/disclosures development by creating an account on GitHub.GitHub
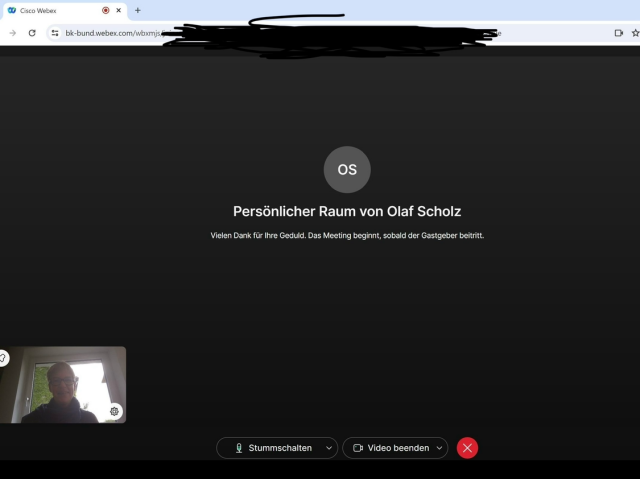
Olaf Scholz' Webex-Meetingraum ist nicht mehr erreichbar.
Ja: der an sich war kein großes Sicherheitsrisiko, denn natürlich kann Olaf Scholz immer noch selbst entscheiden, wen er in seinen Raum hineinlässt oder rauswirft.
ABER: diese persönlichen Meetingräume leaken eine enscheidende Information, die mir heute geholfen hat, einige #Webex -Meetings zu besuchen, zu denen ich nicht eingeladen war.
Dauert noch ein paar Tage, bis alles aufgeräumt ist. Dann schreibe ich euch das auf.
#Cybersecurity
I'm looking to borrow (it's $200 and I'm not buying it) a copy of an extremely niche book from a law school library for a week or so. It's called "Cybersecurity and the Courthouse: Safeguarding the Judicial Process".
It should be very useful for all of my recent #cybersecurity work in that area (see https://github.com/qwell/disclosures/).
If you, dear reader, have access to such things, I'd like to have a chat to see what we can figure out.
Boosts highly appreciated.

GitHub - qwell/disclosures: List of vulnerability disclosures
List of vulnerability disclosures. Contribute to qwell/disclosures development by creating an account on GitHub.GitHub
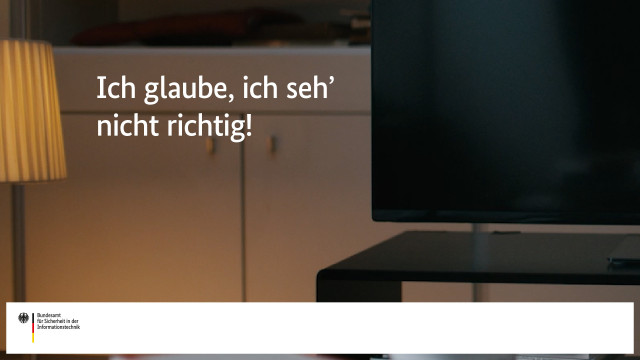
Cyberkriminelle als ungebetene Gäste beim gemütlichen Abend vor dem smarten Fernseher? 📺 Das wollt ihr nicht! Mit unseren Tipps, auf einfachabsichern.de, sorgt ihr dafür, dass Spione nur im Film Ziele ausspähen und nicht in euren privaten Daten schnüffeln.
https://www.zeit.de/digital/datenschutz/2024-05/bundeswehr-webex-sicherheitsluecke-it-sicherheit
#Cybersecurity #bundeswehr
Bundeswehr: Jeder konnte sie finden
Recherchen von ZEIT ONLINE offenbaren eine Sicherheitslücke bei der Bundeswehr und der Bundesregierung: Wer wann zu einem Videocall einlud, ließ sich öffentlich einsehen.Eva Wolfangel (ZEIT ONLINE)
#Sweden has noticed that #cash is indispensable in the face of increasing #cyberwarfare.
#future #technology #money #economy #cybewar #cybercrime #cybersecurity #war #security #backup #system #news #bankster
Years later, #Marriott admits data were not encrypted before its 2018 #databreach. Now what?
Did they get insurance reimbursement because their claim said the data had been encrypted? Will #SEC find they made a material misrepresentation to consumers and investors?
Will people who didn't try to sue them claim they had relied on Marriott's statement and they now want to sue them?
Lots of questions, including when did they first find out that the data had not been encrypted and why didn't they find out and disclose it sooner?
Great reporting by Evan Schuman:
https://www.csoonline.com/article/2096365/marriott-admits-it-falsely-claimed-for-five-years-it-was-using-encryption-during-2018-breach.html

Marriott admits it falsely claimed for five years it was using encryption during 2018 breach
Marriot revealed in a court case around a massive 2018 data breach that it had been using secure hash algorithm 1 and not the much more secure AES-1 encryption as it had earlier maintained.Evan Schuman (CSO Online)
yeah this is pissing me off as I’m one of the larger cybersecurity creators on TikTok at 368,000 followers. It’s still how everyone finds my mastodon, twitch, and soon YouTube. It’s still also 80% of my revenue for my content creation LLC between shop and content payouts.
I’ve been on the platform since the pandemic started and any concerns we have about TikTok were already said about Meta and others
BREAKING: #Israeli private investigator arrested for cyberespionage on behalf of American PR firm.
Caught by UK under #RedNotice from 🇺🇸US while boarding a flight.
BIG TWIST in a wild case that began w/our @citizenlab investigation into indian hack-for-hire group #belltrox
Sound familiar?
Because Amit Forlit is the *second* PI from #Israel arrested in similar way for this case.
First = convicted.
#hacking #cybersecurity #infosec #malware #espionage #intelligence
If you use Dropbox you should probably change your password.
Headline: #Dropbox Hacked! Threat Actor Accessed Passwords and Phone Numbers
Snippet: A quick analysis revealed that a threat actor had broken in to access customer information such as emails, usernames, phone numbers and hashed passwords, as well as general account settings and certain authentication information (API keys, OAuth tokens, and multi-factor authentication).
#Privacy #Security #Cybersecurity

Dropbox Hacked! Threat Actor Accessed Passwords and Phone Numbers
File hosting service Dropbox says a threat actor breached its e-signature service and accessed customer data, including phone numbers and passwords.Hot for Security
Oh, great. Computer security researchers have developed a proof-of-concept for a type of ransomware that would act when you try to *upload* a file. It would be able to encrypt any files in the folder you uploaded from, and any subfolders of it.
This is a proof-of-concept; the researchers have not seen any such attacks in the wild. But stay careful out there, okay?
Affects Chrome and Edge, but *not* Firefox or Safari!
#security #cybersecurity #malware #ransomware

Cybersecurity researchers spotlight a new ransomware threat – be careful where you upload files
Modern web browsers are increasingly becoming like virtual computers, able to send email and play music and videos. The downside is it’s a new way for hackers to get into your computer.The Conversation
I don't think I have many Fediverse connections to the #cybersecurity community in #Sweden, but maybe this can get boosted by someone who does?
A friend just left their job (for reasons unrelated to the position), and in a moment of weakness, as the only one around with my own Fediverse server, I may have volunteered to see if anyone wants to #GetFediHired as their replacement. Technical cybersecurity, incident response, mostly Windows, Swedish language proficiency and in-person attendance (mid-southern Sweden) required. https://liu.se/jobba-pa-liu/lediga-jobb/23904
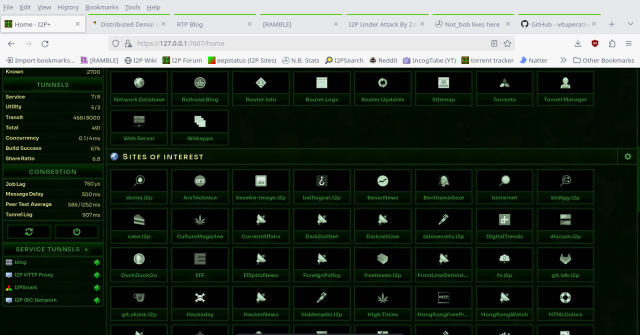
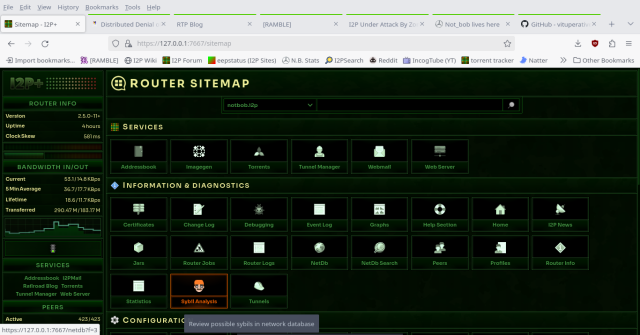
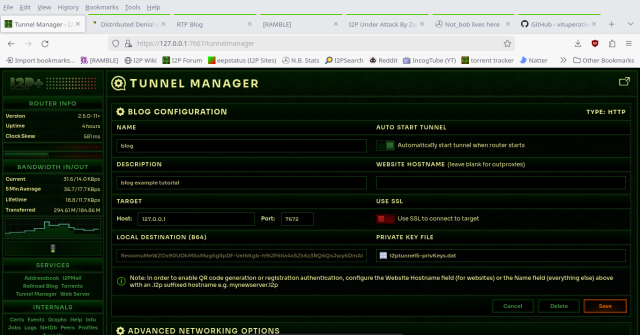
#Networks like #I2P serve useful to #OSINT #investigations, #Journalism, and #activism (#clearnet conns can be more private using #outproxy in I2P).
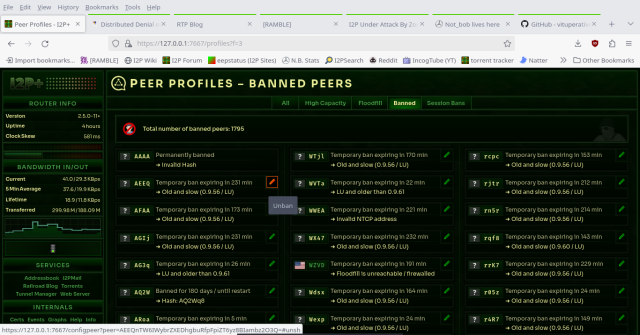
You can customize your routing experience, even change number of hops, banning and unbanning routers based on suspicious behavior! 😎
💡 TIP: take advantage of using both I2P & #Tor browser set up - spreading the risk to personal #privacy / #anonymity (+ avoid blocks).
Right now I2P is under attack: help by running i2p!
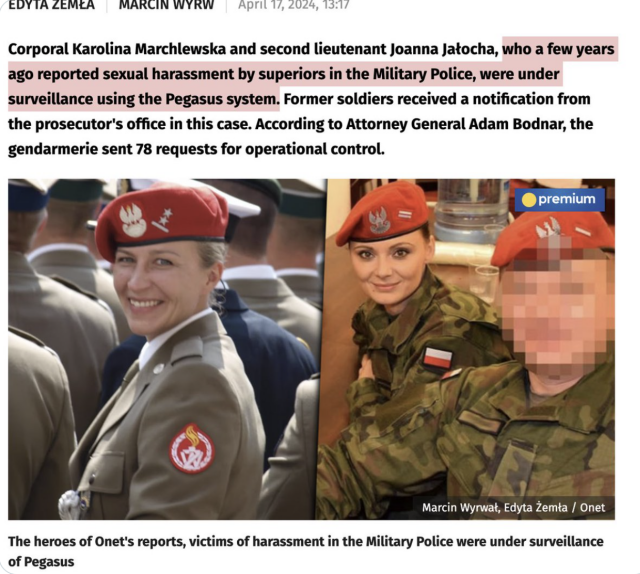
NEW: female army officers that reported sexual harassment... were hacked with #Pegasus.
Official confirmations from #Poland's AG keep shedding light on more apparent spyware abuses by past gov.
Link [in PL]: https://wiadomosci.onet.pl/kraj/zglosily-molestowanie-w-zandarmerii-wojskowej-byly-inwigilowane-pegasusem/dylyrsv
#Poland #spyware #cybersecurity #infosec #hacking #malware #polska #polish #surveillance #intelligence
Bohaterki reportaży Onetu, ofiary molestowania w Żandarmerii Wojskowej, były inwigilowane Pegasusem
Kapral Karolina Marchlewska i podporucznik Joanna Jałocha, które kilka lat temu zgłosiły molestowanie seksualne przez przełożonych w Żandarmerii Wojskowej, były inwigilowane za pomocą systemu Pegasus.IAB
🚨 I2P Is Under DDoS Attack By Zombie Routers
#I2P #networking #infosec #cybersecurity #HumanRights #Journalism #activism #surveillance #Privacy #Sybil #ddos #dos #video #proxy #encryption #crypto #e2ee
Watch In I2P
http://invidious.qwik.i2p/watch?v=XfVdxbtTZ5A
https://tube.tchncs.de/w/fMpkjUnNcaKqPchXUPkgV9

🚨 I2P Under Attack By Zombies! 😮
I2P Network Is Currently Under Heavy DDoS Attack (Distributed Denial Of Service) By Spoofed Routers, Spawning By The Thousands - Some Locations Spinning Up 100+ Routers In A Single Hour. Networks L...tchncs
#Windows #vulnerability reported by the #NSA exploited to install Russian #malware
When Microsoft patched the vulnerability in October 2022—at least two years after it came under #attack by the Russian hackers—the company made no mention that it was under active exploitation.
#patch #update #exploit #Russia #security #CyberSecurity #news #os #software #hack #hacker

Windows vulnerability reported by the NSA exploited to install Russian malware
Microsoft didn't disclose the in-the-wild exploits by Kremlin-backed group until now.Ars Technica
"Citizen, leave a copy of your home keys at the police station."
Hmm, people won't like that.
How about, "home-builders have a social responsibility ...[and must give police copies of all house keys]"
Much better.
#Europol taking another stab at the encryption fight.
#Encryption #privacy #infosec #cybersecurity #europe #surveillance
Advanced #Phishing Kit Adds #LastPass Branding for Use in Phishing Campaigns
Threat actors using phishing kits are pretending to be LastPass in phone calls and emails to steal user credentials.
Actual phishing site: “help-lastpass[.]com”
Shortened URL Embedded in Email: shorturl[.]at/glvT0
Phishing Email Subject Line: We’re here for you
Spoofed Sender: Shows as LastPass Support <support@lastpass>