Search
Items tagged with: Infosec
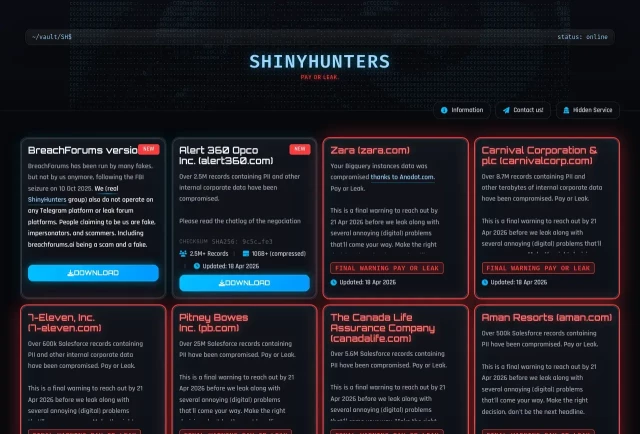
🚨New ransom group blog posts!🚨
Group name: shinyhunters
Post title: Alert 360 Opco Inc. (alert360.com)
Info: cti.fyi/groups/shinyhunters.ht…
Group name: shinyhunters
Post title: Carnival Corporation & plc (carnivalcorp.com)
Info: cti.fyi/groups/shinyhunters.ht…
Group name: shinyhunters
Post title: National Railroad Passenger Corporation (amtrak.com)
Info: cti.fyi/groups/shinyhunters.ht…
Group name: shinyhunters
Post title: Kemper Corporation
Info: cti.fyi/groups/shinyhunters.ht…
Group name: shinyhunters
Post title: McGraw Hill, Inc. (mheducation.com)
Info: cti.fyi/groups/shinyhunters.ht…
Group name: shinyhunters
Post title: Abrigo, Inc.
Info: cti.fyi/groups/shinyhunters.ht…
#ransomware #cti #threatintelligence #cybersecurity #infosec
shinyhunters Ransomware Group
Track shinyhunters ransomware group activity and threat intelligence.CTI.FYI
RE: infosec.exchange/@SecureOwl/11…
Been getting some pretty intense looks when telling people that just because a company *claims* to have deleted your data, it doesn’t mean that it’s *actually deleted*.
#infosec
FIRST Wraps CVE/VulnCon 2026 with 500+ Attendees, New Product Launches, and Key Vulnerability Management Milestones
Four-day summit in Scottsdale draws global security leaders to advance CVE quality, AI security, and coordinated disclosure.FIRST — Forum of Incident Response and Security Teams
i was quite surprised to discover that no one had registered deleteduser [dot] com, and was curious to see how many emails i'd get if i registered it, assuming many orgs 'delete' logic probably just overwrote the email address with blahblah@deleteduser.com or similar.
The answer, is at least 3 different orgs in the hour that I've owned that domain and been listening for email.
And yes, all of those emails contain the actual PII of the person who has been 'deleted' 
On recommence !
Les sites gouv : du gruyère…
⋅ Gros coup dur pour l'Éducation nationale, qui confirme ce mardi soir avoir été victime d'une nouvelle cyberattaque, qui expose les données d'élèves liées à ÉduConnect.
− clubic.com/actualite-608995-no…

Nouveau piratage au ministère de l'Éducation nationale, les données des élèves volées par les hackers
C'est un gros coup dur pour l'Éducation nationale, qui confirme ce mardi soir avoir été victime d'une nouvelle cyberattaque, qui expose les données d'élèves liées à ÉduConnect.Alexandre Boero (Clubic.com)
It doesn't just live on. It's thriving because criminals know they operate in a reactionary environment. It's leverage, and it's working and will continue to works so long as the crisis management model remains the same.
Security Boulevard: Ransomware Lives On, Blending Hacktivism and Crime, Fueled by AI securityboulevard.com/2026/04/… #infosec #ransomware

Ransomware Lives On, Blending Hacktivism and Crime, Fueled by AI - Security Boulevard
Ransomware will never die, will it? In fact, it’s more powerful than ever thanks to GenAI and creative operators that evolve techniques.Teri Robinson (Security Boulevard)
RE: flipboard.com/@404media/404-me…
If you think there's any chance that law enforcement might ever be interested in the content of your Signal chats, and you don't want them to have access to them, then setting up disappearing messages is necessary but not sufficient. You also need to go into the Signal settings and either disable notifications completely or set them to show "No name or message" so the content won't be capture and preserved in the phone's notification database.
#infosec #privacy #OpSec "#antifa"

FBI Extracts Suspect’s Deleted Signal Messages Saved in iPhone Notification Database
The case was the first time authorities charged people for alleged “Antifa” activities after President Trump designated the umbrella term a terrorist …404 Media - Joseph Cox
Oh boy…
edition.cnn.com/2026/04/08/chi…
> A [cyberthreat actor] has allegedly stolen a massive trove of sensitive data – including highly classified defense documents and missile schematics – from a state-run Chinese supercomputer
> The dataset, which allegedly contains more than 10 petabytes of sensitive information, is believed by experts to have been obtained from the National Supercomputing Center (NSCC) in Tianjin
🧵
hey so this is probably completely pointless but: looking for a job (NZ or fully remote willing to hire a kiwi) in SRE, security, or linux/Unix system administration. 15 years expereince administering Linux and Unix boxes, intermediate level of experience working with docker compose and containerisation and container security. No prior job experience unfortunately, all those 15 years were mostly personal projects and small-scale stuff for friends. Currently running an entire multi-machine personal cloud infrastructure with a demonstration of all the services I have running at status.highenergymagic.net. Entirely willing to accept entry-level job placements, no expectation of being paid a lot or anything, just want to be doing something and move the needle a little on my current "being broke" status. #fedihired #infosec #cybersecurity #linux #unix #docker #sre #DevOps
Please boost for reach, any job offers please DM me.
If this doesn't convince you big tech has too much control, I don't know what will.
h/t @zackwhittaker
techcrunch.com/2026/04/08/vera…
#infosec #privacy #TechIsShitDispatch
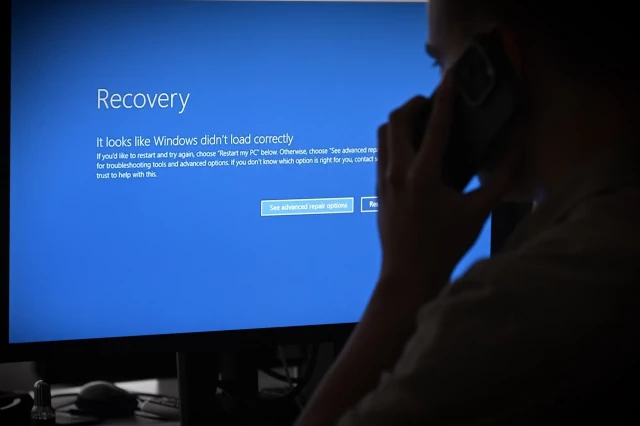
Developer of VeraCrypt encryption software says Windows users may face boot-up issues after Microsoft locked his account | TechCrunch
The maker of the popular open source file encryption software VeraCrypt said Microsoft locked his online account, which may prevent device owners from booting up their computers.Zack Whittaker (TechCrunch)
There used to be a time when building out a botnet required *some* work – writing exploits, taking over devices, obscuring the purpose of the executable, etc.
Not any more!
Instead of "malware", call it an "AI agent" and people will just happily install it on their devices with full root privileges!
github.com/jgamblin/OpenClawCV…
Bam! RCE by asking nicely.
🧵
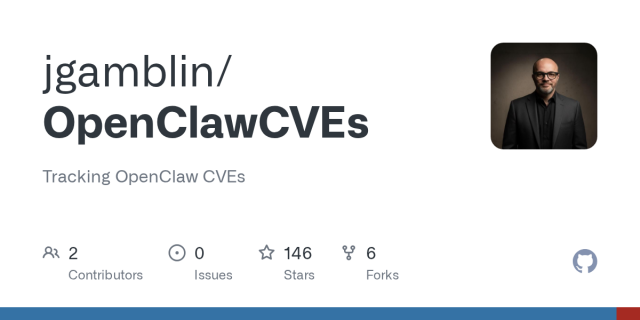
GitHub - jgamblin/OpenClawCVEs: Tracking OpenClaw CVEs
Tracking OpenClaw CVEs. Contribute to jgamblin/OpenClawCVEs development by creating an account on GitHub.GitHub
Oh look. Drama. With a meta product.
🙄
techcrunch.com/2026/04/01/what…

WhatsApp notifies hundreds of users who installed a fake app made by government spyware maker | TechCrunch
The Meta-owned company said it identified around 200 users who were tricked into installing a fake version of WhatsApp that was actually Italian-made spyware.Lorenzo Franceschi-Bicchierai (TechCrunch)
EDIT: @rysiek has an explanation about the shady things LinkedIn is doing. He explains it far better than I did:
mstdn.social/@rysiek/116337205…
LinkedIn/Microsoft are definitely NOT to be trusted. But I realize phrasing is important. So I’m moderating my own post. I apologize if this was misconstrued.
But I subjectively believe there is a high likelihood that LinkedIn is doing nefarious things with this data.
#BrowserGate #LinkedIn #InfoSec #OpSec #Privacy #YouAreTheProduct #Microsoft
Michał "rysiek" Woźniak · 🇺🇦 (@rysiek@mstdn.social)
There is a fresh thing going around about LinkedIn scanning extensions installed in Chrome/Chromium: https://browsergate.Michał "rysiek" Woźniak · 🇺🇦 (Mastodon 🐘)
Apparently #LinkedIn if silently collecting data on every extension you use every time you visit the site. Which it then uploads, with your identity attached to it.
This is absolutely horrifying. Literally, people should go to jail over this.
#infosec #privacy
browsergate.eu/
LinkedIn Is Illegally Searching Your Computer
Microsoft is running one of the largest corporate espionage operations in modern history. Every time any of LinkedIn’s one billion users visits linkedin.BrowserGate
LinkedIn Is Illegally Searching Your Computer
#tech #technology #BigTech #IT #enshittification #microslop #microsoft #LinkedIn #social #media #SocialMedia #data #security #safety #InfoSec #internet #web
LinkedIn Is Illegally Searching Your Computer
Microsoft is running one of the largest corporate espionage operations in modern history. Every time any of LinkedIn’s one billion users visits linkedin.BrowserGate
NodeJS, for all the brilliant projects out there leaning on it, has a supply chain that might as well run the length of a dark alley permanently at 2am in the club district.
thehackernews.com/2026/03/axio…
Anyway, hope none of you good people are affected by this latest pox

Axios Supply Chain Attack Pushes Cross-Platform RAT via Compromised npm Account
Axios 1.14.1 and 0.30.4 injected malicious plain-crypto-js@4.2.1 after npm compromise on March 31, 2026, deploying cross-platform RAT malware.The Hacker News
Watching the livestream of the Artemis II launch, I just witnessed one of the astronauts type in the password on their tablet while sitting in the capsule on camera.
#ArtemisII #Artemis #Artemis2 #NASA #InfoSec #cybersecurity #OpSec #Privacy #SpaceExploration
Claude Code source leak reveals how much info Anthropic can hoover up about you and your system
"Anthropic's Claude Code lacks the persistent kernel access of a rootkit. But an analysis of its code shows that the agent can exercise far more control over people's computers than even the most clear-eyed reader of contractual terms might suspect. It retains lots of your data and is even willing to hide its authorship from open-source projects that reject AI."
theregister.com/2026/04/01/cla…
Claude Code source leak reveals how much info Anthropic can hoover up about you and your system
: If you loved the data retention of Microsoft Recall, you'll be thrilled with Claude CodeThomas Claburn (The Register)
forbes.com/sites/the-wiretap/2…
TLDR If you access multiple Google accounts from the same device, and the cops know about one of the accounts and ask Google the right questions, Google will tell the cops about the other accounts.
The general lesson here is one we already know: if you have any sort of account you don't want linked to you, you can't ever access it from a device or network connection you use other accounts on.
Caveat usor.
#infosec #OpSec #Google

Federal cyber experts called Microsoft's cloud a "pile of shit," approved it anyway
One Microsoft product was approved despite years of concerns about its security.ProPublica (Ars Technica)
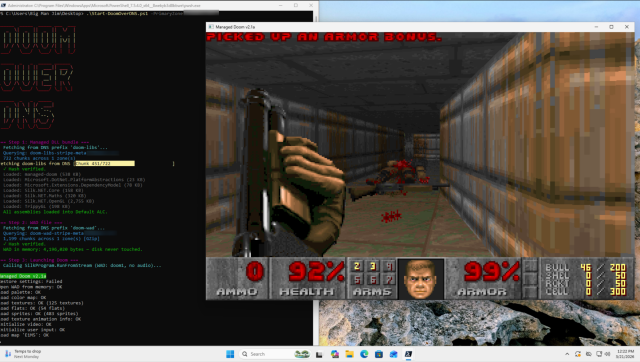
In today's episode of "Can It Run Doom": DNS fucking TXT records.
Some absolute madlad (cough Adam Rice cough) compressed the entire shareware DOOM WAD, split it into around 1,964 chunks, shoved them into Cloudflare TXT records, and wrote a PowerShell script that reassembles and runs the whole goddamn game from DNS queries alone. Nothing touches disk. The DLLs are in DNS. THE FUCKING DLLS ARE IN DNS.
RFC 1035 was written in 1987. Those engineers are spinning in their graves fast enough to generate municipal power.
Bonus: this is a fully functional globally-distributed covert data exfil channel that your NGFW will never fucking see if you're not doing deep DNS inspection. Sleep well.
blog: blog.rice.is/post/doom-over-dn…
repo: github.com/resumex/doom-over-d…
Also lmao @ every blue team that has never once looked at their DNS query volume. How's that DLP policy working out for you.
It was always DNS.
#infosec #dns #doom #itisalwaysdns
Can it Resolve DOOM? Game Engine in 2,000 DNS Records – blog.rice.is
To a guy like me, Crazy Frog is just a frog.blog.rice.is
The correct way to run a headline for this story. The reg does not disappoint
#uspol #routers #surveillance #privacy #nationalsecurity #cybersecurity #infosec #cisco #theregister
#TSA Tipped Off #ICE Agents Before Arrests at #SanFrancisco #Airport
Transportation Security Administration officials told ICE that a mother & daughter under a detention order had planned to fly domestically, federal documents show.
#law #entrapment #immigration #Trump #privacy #InfoSec #DueProcess
nytimes.com/2026/03/24/us/tsa-…
Supply-chain attack on litellm
"At 10:52 UTC on March 24, 2026, litellm version 1.82.8 was published to PyPI. The release contains a malicious .pth file (litellm_init.pth) that executes automatically on every Python process startup when litellm is installed in the environment."
futuresearch.ai/blog/litellm-p…
#genai #llms #litellm #infosec #python
Supply Chain Attack in litellm 1.82.8 on PyPI
litellm version 1.82.8 on PyPI contains a malicious .pth file that harvests SSH keys, cloud credentials, and secrets on every Python startup, then attempts lateral movement across Kubernetes clusters.Callum McMahon (FutureSearch)
Addressing the #LiteLLM supply chain incident:
All #SakuraSky managed production environments are unaffected by the v1.82.7/8 compromise.
Our infrastructure is a "Zero-Value Target." Using #OIDC and Just-in-Time key injection, we ensure that even if a library is breached, it finds an "empty room"- no static keys or .env files to steal.
We’re also accelerating our Sentinel framework for deeper AI agent governance.
Details: sakurasky.com/blog/security-ad…
#InfoSec #AI #SupplyChainSecurity #DevSecOps
Security Advisory: Resilience in the Face of the LiteLLM Supply Chain Incident
Sakura Sky confirms zero impact from the LiteLLM supply chain hack (v1.82.7/8). Learn how our 'Zero-Value Target' architecture and Sentinel framework protect managed AI environments.www.sakurasky.com
Supply Chain Attack Targets litellm Library to Steal Cloud Credentials and Hijack Kubernetes Clusters
TeamPCP compromised the litellm Python library to distribute malicious versions (1.82.7 and 1.82.8) that harvest cloud credentials, SSH keys, and Kubernetes secrets. The attack uses a persistent backdoor and lateral movement toolkit to compromise entire clusters and steals data to attacker-controlled infrastructure.
**If you use litellm in any project, check immediately whether you have version 1.82.7 or 1.82.8 installed. If so, isolate the affected systems, revert to a clean version, and rotate every credential on those machines (SSH keys, cloud tokens, API keys, database passwords, crypto wallets, all of it). Because this attack can spread through other tools that depend on litellm, also audit your broader Python environments and CI/CD pipelines for these versions, remove any persistence files (sysmon.py, sysmon.service), and check Kubernetes clusters for unauthorized pods.**
#cybersecurity #infosec #advisory #vulnerability
beyondmachines.net/event_detai…
🐛 NEW SECURITY CONTENT 🐛
💻 macOS Tahoe 26.4 - 77 bugs fixed
support.apple.com/en-us/126794
💻 macOS Sequoia 15.7.5 - 60 bugs fixed
support.apple.com/en-us/126795
💻 macOS Sonoma 14.8.5 - 54 bugs fixed
support.apple.com/en-us/126796
📱 iOS and iPadOS 26.4 - 38 bugs fixed
support.apple.com/en-us/126792
🥽 visionOS 26.4 - 29 bugs fixed
support.apple.com/en-us/126799
📱 iOS and iPadOS 18.7.7 - 25 bugs fixed
support.apple.com/en-us/126793
⌚ watchOS 26.4 - 22 bugs fixed
support.apple.com/en-us/126798
📺 tvOS 26.4 - 17 bugs fixed
support.apple.com/en-us/126797
⌚ watchOS 8.8.2 - no CVE entries
⌚ watchOS 5.3.10 - no CVE entries
#apple #cybersecurity #infosec #security #ios
About the security content of iOS 26.4 and iPadOS 26.4 - Apple Support
This document describes the security content of iOS 26.4 and iPadOS 26.4.Apple Support
🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉🎉
tomshardware.com/software/oper…
#Infosec #GrapheneOS #AgeVerification #Linux #Mastodon