Search
Items tagged with: Security
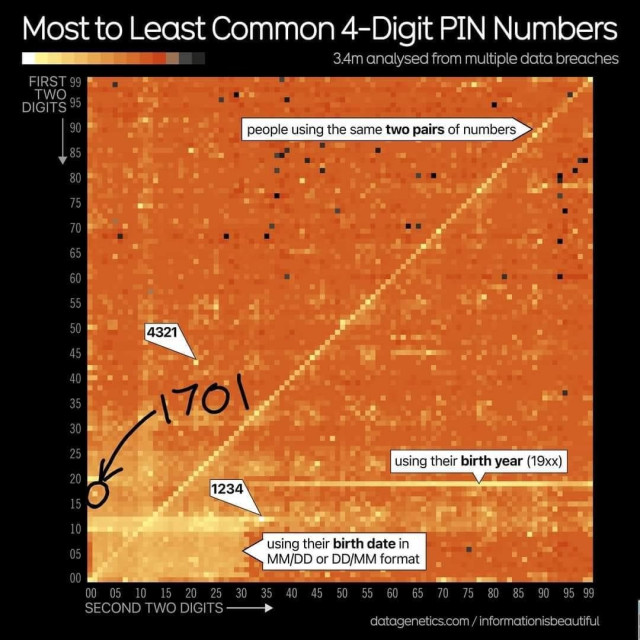
From a human behavior analysis standpoint, this image is absolutely fascinating. There is so much information about human behavior that can be extracted from the data represented here
EDIT: OMFG 1701 IS THE DESIGNATION OF THE STAR SHIP ENTERPRISE (NCC-1701). TREKKIES WHY ARE YOU LIKE THIS?!? 
Why is #Mozilla collecting our #search data?
source: https://blog.mozilla.org/en/products/firefox/firefox-search-update/
Sensitive topics, like searching for particular health care services, are categorized only under broad terms like health or society. Your search activities are handled with the same level of confidentiality as all other data regardless of any local laws surrounding certain health services.
Hello Mozilla, I use Firefox because my privacy is important to me. The best security is still achieved if you don't collect the data. That is why I will use a fork that does not collect search data. It would be nice if Mozilla took user privacy more seriously.
#privacy #news #browser #web #internet #firefox #security #cybersecurity #surveillance #statistics #bigdata #bigbrother

See what’s changing in Firefox: Better insights, same privacy
We’re ramping up our efforts to enhance search experience by developing new features like Firefox Suggestions.Mozilla (The Mozilla Blog)
If you're using GNU/Linux. Please use opensnitch, it's criminally underrated. It notifies you of network requests made in real time, and you can choose to allow them or not (it comes with a lot of filtering options as well): https://github.com/evilsocket/opensnitch
#privacy #infosec #linux #foss #security

GitHub - evilsocket/opensnitch: OpenSnitch is a GNU/Linux interactive application firewall inspired by Little Snitch.
OpenSnitch is a GNU/Linux interactive application firewall inspired by Little Snitch. - evilsocket/opensnitchGitHub
Do you want to learn how to setup an air-gapped #Nextcloud for maximum privacy and data protection?
Join me on May 22nd at 9 am EDT / 3 pm CEST on a free webinar to learn about air-gapped Nextcloud:
🔍 Critical factors to consider
🛡️ Four customizable air-gapped setups
🔧 Setting up air-gapped Nextcloud instances
💼 Best practices for Nextcloud maintenance
Register for free:
https://bit.ly/3QB2dlv
#OpenSource #GovTech #Security #CyberSecurity #infosec #privacy #sysadmin #datasecurity
![[Webinar] Beyond Secure: Air-gapped Nextcloud for highly confidential data](https://friendica.hellquist.eu/photo/preview/640/2662225)
[Webinar] Beyond Secure: Air-gapped Nextcloud for highly confidential data
Join us to learn how you can set up air-gapped Nextcloud for highly confidential data ideal for military, government, and large enterprises.Nextcloud
#Google #Cloud accidentally deletes #UniSuper’s online #account due to ‘unprecedented #misconfiguration’
While UniSuper normally has duplication in place in two geographies, to ensure that if one service goes down or is lost then it can be easily restored, because the fund’s cloud subscription was deleted, it caused the deletion across both geographies.
#fail #economy #security #backup #problem #omg #wtf #news

Google Cloud accidentally deletes UniSuper’s online account due to ‘unprecedented misconfiguration’
Super fund boss and Google Cloud global CEO issue joint statement apologising for ‘extremely frustrating and disappointing’ outageJosh Taylor (The Guardian)
The #Biden admin has concluded it is “reasonable to assess” that #Israel’s military campaign in #Gaza has violated #InternationalLaw, but has not found specific instances that would justify the withholding of #military aid, #State Dept told #Congress Fri.
#LawsOfWar #InternationalHumanitarianLaw #HumanRights #Law #Palestinians #HumanitarianCrisis #MiddleEast #geopolitics #Security
https://www.nytimes.com/live/2024/05/10/world/israel-gaza-war-hamas-rafah/biden-israel-us-weapons-gaza?smid=nytcore-ios-share&referringSource=articleShare&sgrp=c-cb
Who controls the tech stack❓
When choosing a secure solution for your data, this one of the most important questions❗
Here's why: ➡️ https://tuta.com/blog/what-is-a-tech-stack
#security #technology #opensource #foss
What is a tech stack and how Tuta makes sure it's secure
Open Source audited technologies and self-built solutions give the Tuta team full control over their tech stack - an important factor when it comes to security.Tutanota
Secure PDF Viewer app version 19 released:
https://github.com/GrapheneOS/PdfViewer/releases/tag/19
See the linked release notes for a summary of the improvements over the previous release and a link to the full changelog.
Forum discussion thread:
https://discuss.grapheneos.org/d/12571-secure-pdf-viewer-app-version-19-released
#GrapheneOS #privacy #security #pdf #android

Secure PDF Viewer app version 19 released - GrapheneOS Discussion Forum
GrapheneOS discussion forumGrapheneOS Discussion Forum
"There are no ways to prevent such attacks"
Well that's concerning...
"except when the user's VPN runs on Linux or Android"
Oh. Well then.
Novel attack against virtually all VPN apps neuters their entire purpose
TunnelVision vulnerability has existed since 2002 and may already be known to attackers.Ars Technica
It is always a bad sign when a #democracy bans the #press...
source: https://www.bbc.com/news/world-middle-east-68961753.amp
The Foreign Press Association (FPA) urged the Israeli government to reconsider its decision, saying the shut down of #AlJazeera in the country should be "a cause for concern for all supporters of a free press".
#censorship #war #gaza #problem #journalism #freedom #politics #military #humanrights #security #news

Al Jazeera office raided as Israel takes channel off air
The network denies being a threat to security, and says Israel wants "to cover up its crimes".BBC News
#Sweden has noticed that #cash is indispensable in the face of increasing #cyberwarfare.
#future #technology #money #economy #cybewar #cybercrime #cybersecurity #war #security #backup #system #news #bankster
How to Stop Any Smart TV From Spying on You:
"Smart TVs track your viewing habits using content recognition and voice capture for targeted advertising.
Disconnecting smart TVs from the internet can prevent data tracking, but limits functionality and will require you to use a streaming box for many tasks (which may also track you)"
#News #TV #Privacy #Security
https://www.howtogeek.com/how-to-stop-any-smart-tv-from-spying-on-you-lg-samsung-sony-vizio/?user=cmF2ZW4uY2FAcHJvdG9uLm1l&lctg=9cd17b80cd7d20011df2d51c589bdd9c4cc26e4110d76355b40d8c29d7add1ba

How to Stop Any Smart TV From Spying on You: LG, Samsung, Sony, Vizio
TV manufacturers are hungry for your data.Tim Brookes (How-To Geek)
What Happens When a #Romance #Writer Gets Locked Out of #Google Docs
In March, an aspiring author got a troubling message: All of her works in progress were no longer accessible. What happened next is every writer’s worst fear.
Google never specified which of her 222,000 words was inappropriate.
...
Generally speaking, files containing #violence, #abuse, child sexual abuse material, and gore violate the terms of service for Google Drive and its associated products, like Docs and Sheets.
Now many of you will be thinking, who is stupid enough to store everything in the Google #cloud? The problem is we know that, but many people out there don't. We urgently need to do more educational work and warn people about companies like Google and their practices. Tell all your friends and acquaintances and don't use the clouds of the big corporations.
#news #problem #fail #warning #danger #service #customer #internet #economy #security #wtf #omg #disaster
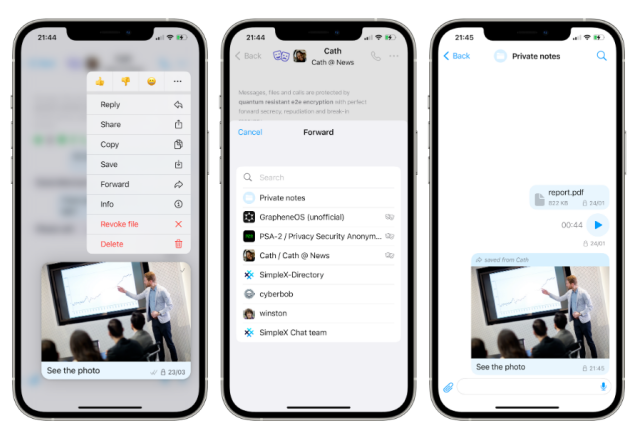
In case you missed it, what's new in the latest release from SimpleX Chat, v5.7:
Quantum resistant end-to-end encryption enabled for all contacts, forward and save messages without revealing the source, in-call sound effects and switching sound sources, and better network connection management.
Coming soon: UI improvements is a major priority.
If you use Dropbox you should probably change your password.
Headline: #Dropbox Hacked! Threat Actor Accessed Passwords and Phone Numbers
Snippet: A quick analysis revealed that a threat actor had broken in to access customer information such as emails, usernames, phone numbers and hashed passwords, as well as general account settings and certain authentication information (API keys, OAuth tokens, and multi-factor authentication).
#Privacy #Security #Cybersecurity

Dropbox Hacked! Threat Actor Accessed Passwords and Phone Numbers
File hosting service Dropbox says a threat actor breached its e-signature service and accessed customer data, including phone numbers and passwords.Hot for Security
Oh, great. Computer security researchers have developed a proof-of-concept for a type of ransomware that would act when you try to *upload* a file. It would be able to encrypt any files in the folder you uploaded from, and any subfolders of it.
This is a proof-of-concept; the researchers have not seen any such attacks in the wild. But stay careful out there, okay?
Affects Chrome and Edge, but *not* Firefox or Safari!
#security #cybersecurity #malware #ransomware

Cybersecurity researchers spotlight a new ransomware threat – be careful where you upload files
Modern web browsers are increasingly becoming like virtual computers, able to send email and play music and videos. The downside is it’s a new way for hackers to get into your computer.The Conversation
Hackers claim to have infiltrated #Belarus’ main #security service
Source: https://apnews.com/article/belarus-cyberattack-kgb-dissent-efc7e6acd9dfe8a118e1d2f526c4d6fa
A Belarusian #hacker activist group claims to have infiltrated the network of the country’s main #KGB security agency and accessed personnel files of over 8,600 employees of the organization, which still goes under its Soviet name.
#hack #news #politics #cyberwar

Hackers claim to have infiltrated Belarus' main security service
A Belarusian hacker activist group claims to have infiltrated the network of the country’s main security agency and obtained access to personal files of over 8,600 staffers of the KGB, the security service that still goes under its Soviet name.YURAS KARMANAU (AP News)

Delta Chat: FAQ
What is Delta Chat? Delta Chat is a new chat app that sends messages via e-mails, encrypted if possible, with Autocrypt. You do not have to sign up anywhere, just use your existing e-mail account w...delta.chat
#Safari on #iOS features device #tracking
source: https://mastodon.social/@mysk/112340023465073147
#Apple recently introduced a new URI scheme so that #iOS users in the #EU can install marketplace apps from the browser. #Safari handles the scheme insecurely leaving users exposed to tracking.
#surveillance #politics #europe #software #security #privacy #news #problem #fail #smartphone #warning
Mysk🇨🇦🇩🇪 (@mysk@mastodon.social)
PSA: #Apple recently introduced a new URI scheme so that #iOS users in the #EU can install marketplace apps from the browser. #Safari handles the scheme insecurely leaving users exposed to tracking.Mastodon
Google is out of their mind. There are so many other options for a "more secure" browser. Especially one that doesn't have Google tied to it.
https://infosec.exchange/@happygeek/112337847581863603
happygeek :unverified: + :verified: = $0 (@happygeek@infosec.exchange)
By me @Forbes: Would you pay $6 a month for a more secure version of Chrome? Google is banking on it. #infosec #Google #Chrome #Enterprise https://www.forbes.Infosec Exchange
#Windows #vulnerability reported by the #NSA exploited to install Russian #malware
When Microsoft patched the vulnerability in October 2022—at least two years after it came under #attack by the Russian hackers—the company made no mention that it was under active exploitation.
#patch #update #exploit #Russia #security #CyberSecurity #news #os #software #hack #hacker

Windows vulnerability reported by the NSA exploited to install Russian malware
Microsoft didn't disclose the in-the-wild exploits by Kremlin-backed group until now.Ars Technica
#CVE-2024-20356: #Jailbreaking a #Cisco appliance to run #DOOM
In this adventure, the Cisco #C195 device family was jailbroken in order to run unintended code. This includes the discovery of a vulnerability in the #CIMC body management controller which affects a range of different devices, whereby an authenticated high privilege user can obtain underlying root access to the server’s #BMC (CVE-2024-20356) which in itself has high-level access to various other components in the system. The end goal was to run DOOM – if a smart fridge can do it, why not Cisco?
source: https://labs.nettitude.com/blog/cve-2024-20356-jailbreaking-a-cisco-appliance-to-run-doom/
#software #security #bug #network #game #news #vulnerability #exploit #hack #hacker
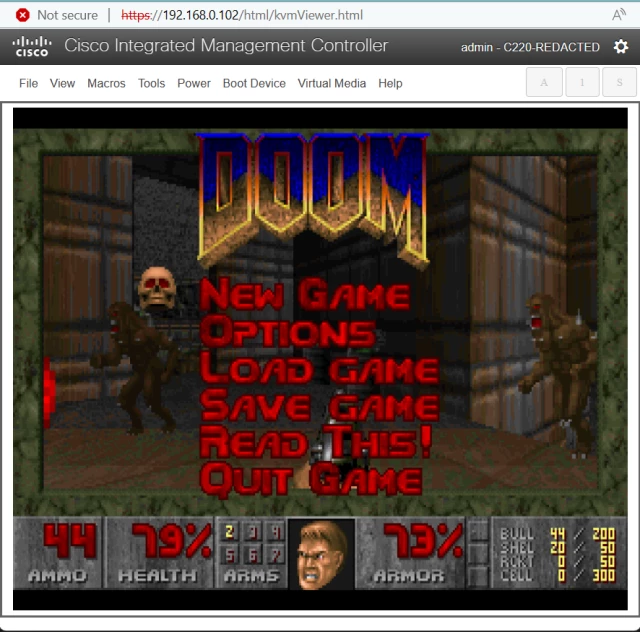
CVE-2024-20356: Jailbreaking a Cisco appliance to run DOOM - LRQA Nettitude Labs
Exploiting remote code execution in Cisco's CIMC management system and jailbreaking the device to run untrusted codeAaron Thacker (LRQA Nettitude Labs)
Friends don't let friends use Discord.
Message History of 600 Million Discord Users Can be Accessed For $5
https://80.lv/articles/message-history-of-600-million-discord-users-can-be-accessed-for-usd5/

Message History of 600 Million Discord Users Can be Accessed For $5
A new report sheds light on a scraping service that lets anyone view your message history across different Discord servers.Theodore McKenzie (80lv)
Advanced #Phishing Kit Adds #LastPass Branding for Use in Phishing Campaigns
Threat actors using phishing kits are pretending to be LastPass in phone calls and emails to steal user credentials.
Actual phishing site: “help-lastpass[.]com”
Shortened URL Embedded in Email: shorturl[.]at/glvT0
Phishing Email Subject Line: We’re here for you
Spoofed Sender: Shows as LastPass Support <support@lastpass>
#Microsoft is a national #security threat, says ex-#WhiteHouse cyber policy director
Source: https://www.theregister.com/2024/04/21/microsoft_national_security_risk/
Microsoft has a shocking level of #control over IT within the US federal #government
#technology #CyberSecurity #economy #politics #software #problem #usa #news

Microsoft is a national security threat, says ex-White House cyber policy director
With little competition at the goverment level, Windows giant has no incentive to make its systems saferBrandon Vigliarolo (The Register)
to me, #biometric unlocking, is unsafe, you see a lot of unauthorised unlocking from restrained, sleeping, dead, or drunken people from either face or fingerprint to unlock a device.
it was established a few years ago that law enforcement in the usa do not need a warrant for biometric unlocking, but need warrant if a password is enabled, to unlock a device.
#phone #thumbprint #court #usa #justice #privacy #security #smartphone #mobile #technology #news #police #surveillance